Provision Users and Groups from Okta
Okta is a cloud-based identity and access management (IAM) platform that centralizes user and customer profiles to enhance security and streamline access. It offers features like multifactor authentication, single sign-on, and lifecycle management to help organizations manage user identities effectively.
QuFabric's Okta integration enhances user management by allowing you to utilize Okta as your identity provider. This integration automates user authentication in your network, adds SSO and MFA support, and simplifies network access management to your applications and resources.
The integration process consists of two stages: first, you’ll set up OpenID Connect (OIDC) to enable Single Sign-On (SSO) from QuFabric's login page using Okta credentials. Next, you’ll configure SCIM (System for Cross-domain Identity Management) to synchronize users and groups smoothly.
Get Started with QuFabric-Okta Integration
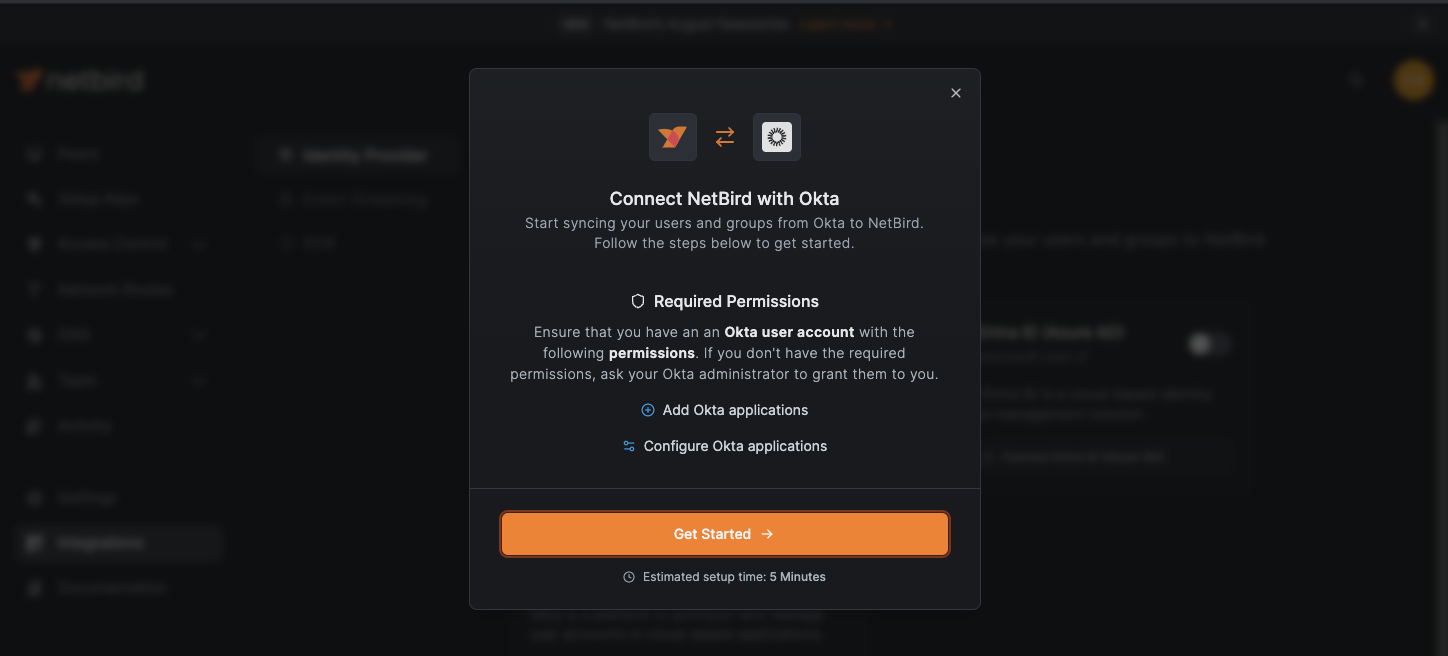
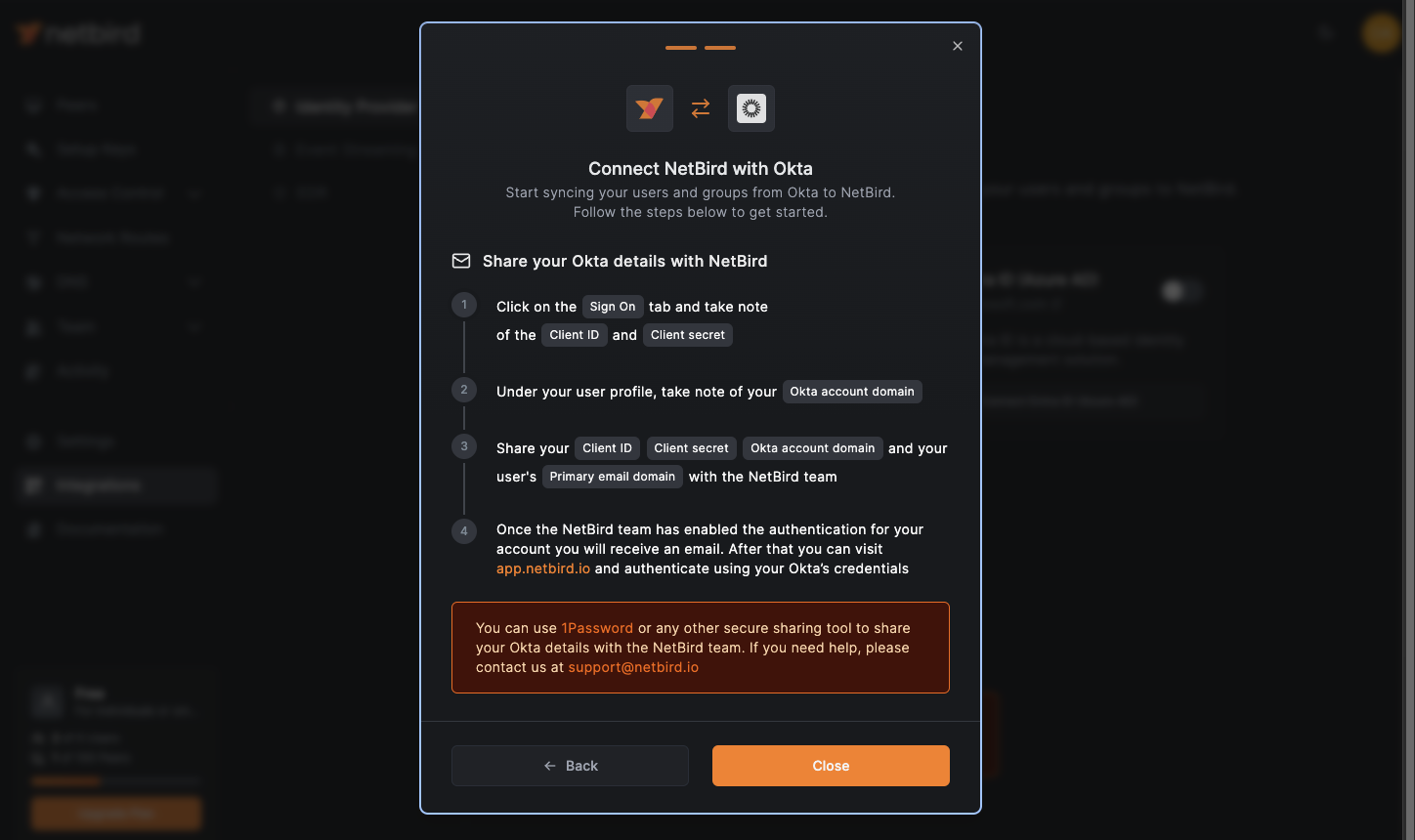
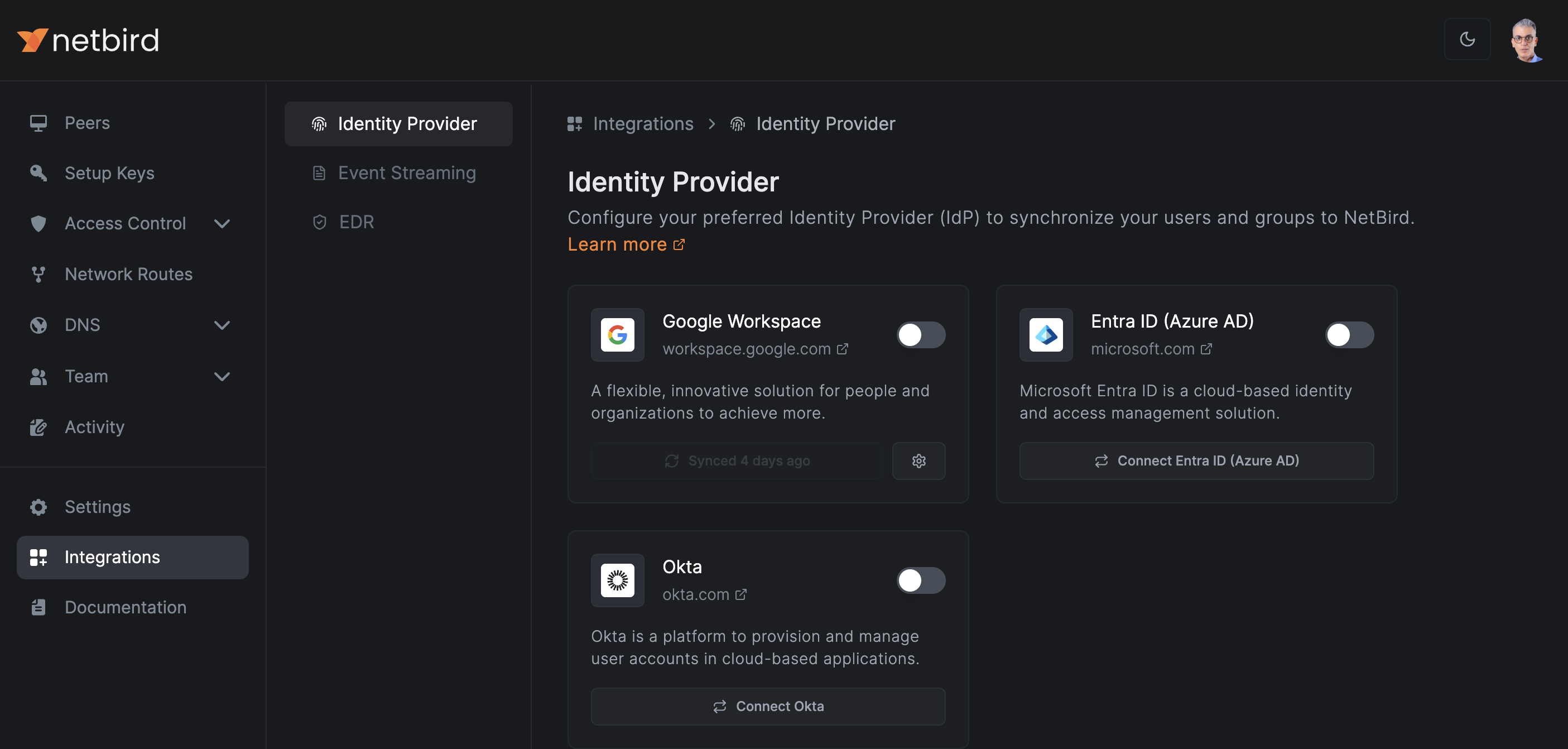
To set up SSO, go to Integrations in the QuFabric admin console's left menu to access the Identity Provider integration page. Click the Connect Okta button to get started with the Okta-QuFabric integration. This will open a pop-up window with detailed instructions on synchronizing QuFabric and Okta.
Prerequisites
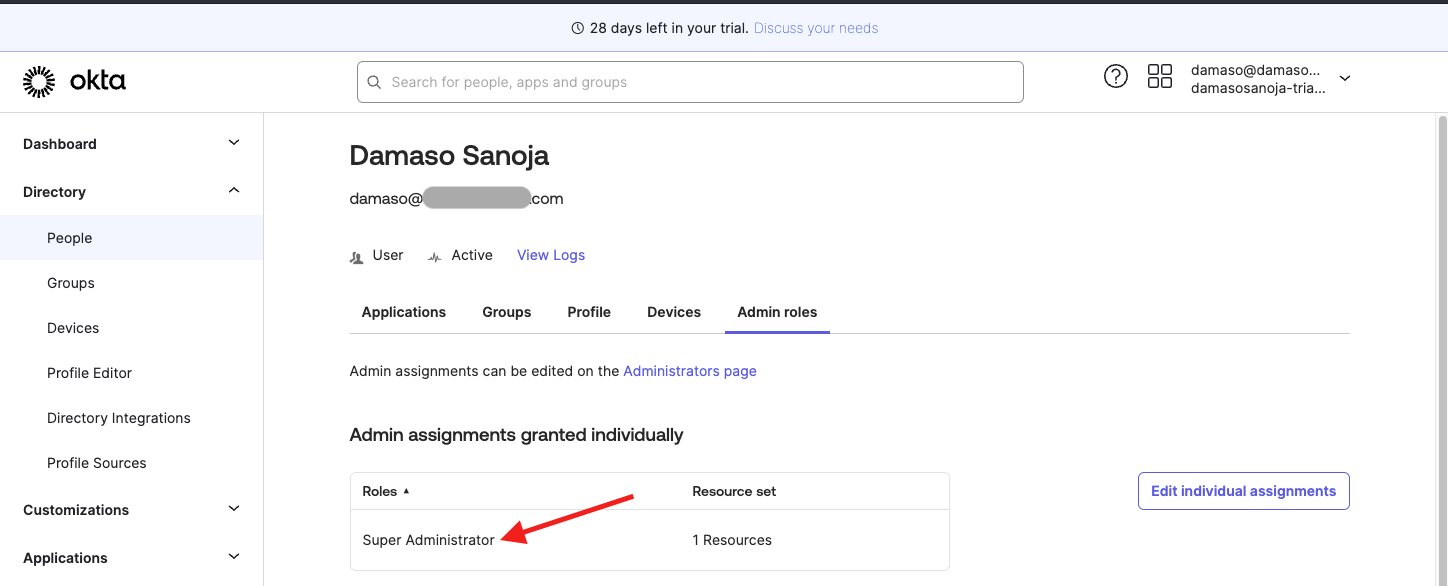
Before you begin the integration process, ensure you have the necessary permissions in Okta. You need an Okta user account with one of the following roles:
- Super Admin
- Org Admin
- Group Admin
To check your user permissions in Okta:
- Log in to your Okta admin dashboard.
- Expand
Peoplein the left menu. - Select your user.
- Navigate to the
Admin rolestab.
Confirm that you have one of the required roles before proceeding with the integration.
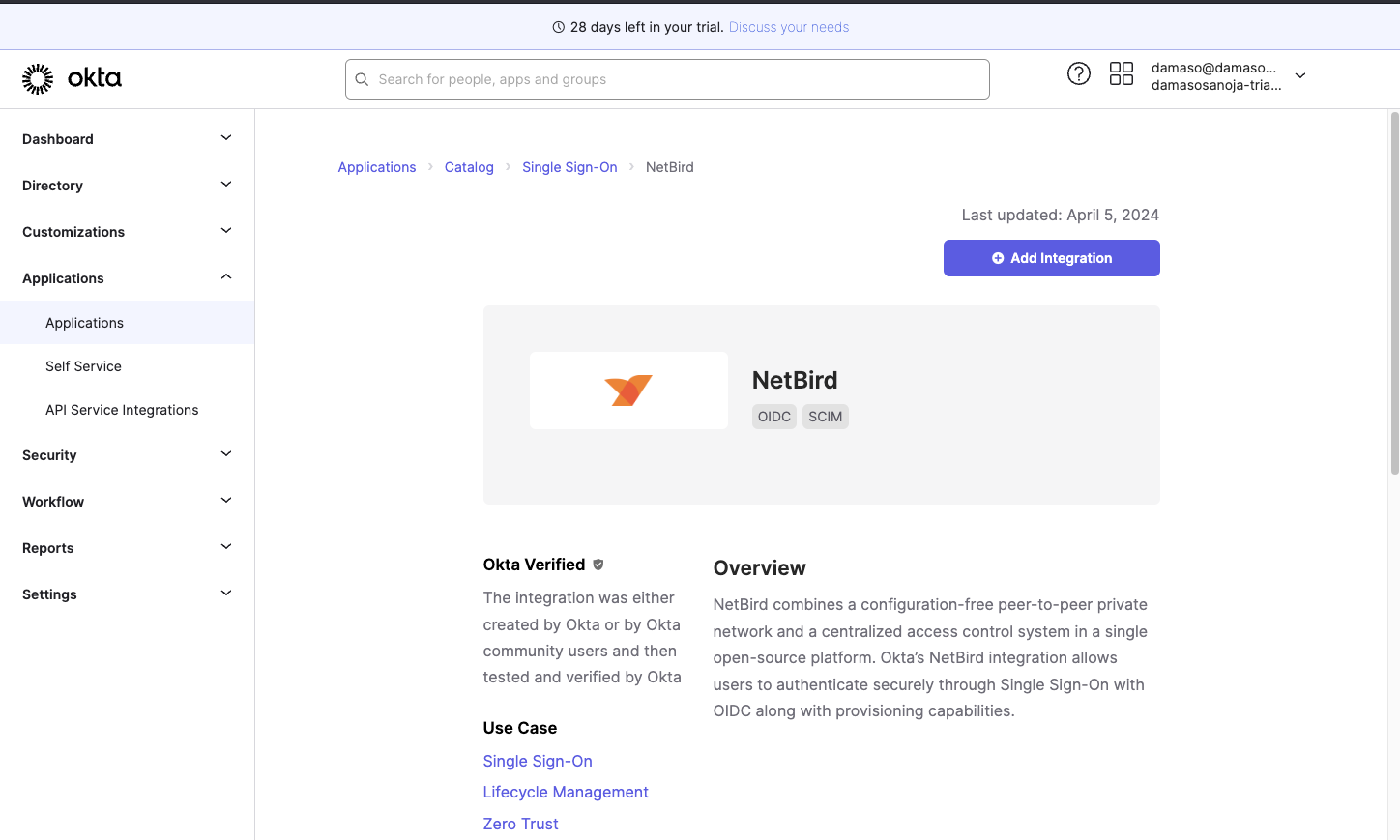
Installing the QuFabric Integration
Once you have the necessary permissions, you can set up the QuFabric application. First, on QuFabric, click Continue → to show a summary of the necessary steps.
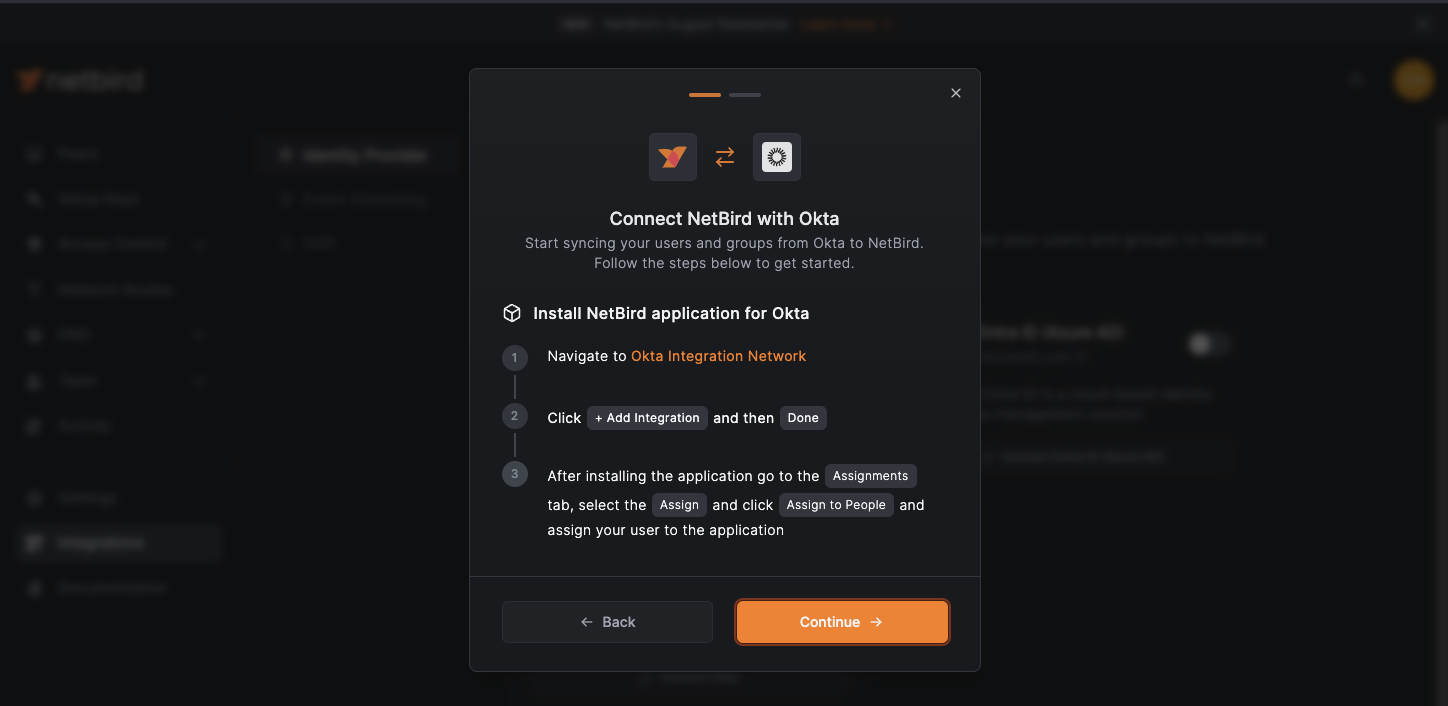
Let's go through them one by one:
- In Okta’s admin dashboard, click
Applicationsin the left menu. - Select
Applicationsfrom the submenu. - Click the
Browse App Catalogbutton.
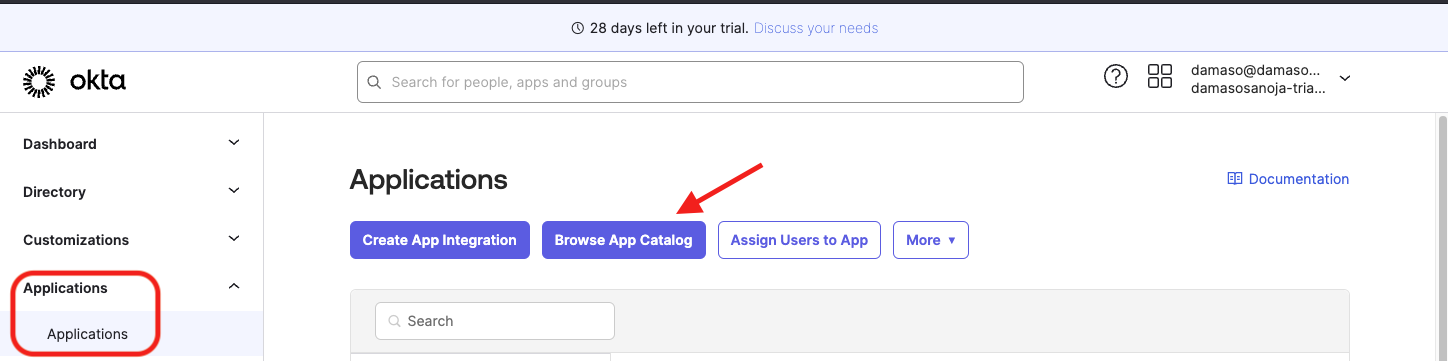
In the app catalog, enter "QuFabric" in the search bar. Then, click the Add Integration button.
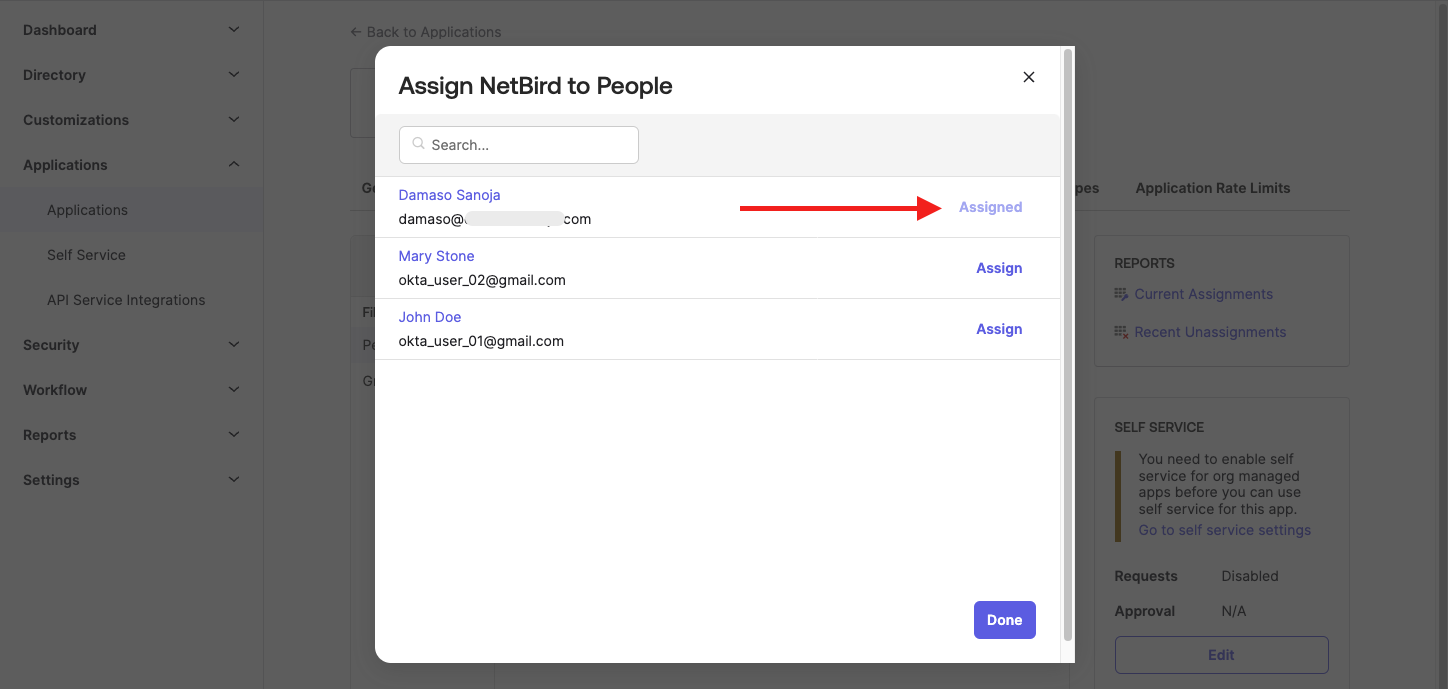
Accept the default application name and click the Done button. On the next screen, click the Assign dropdown and select Assign to People.
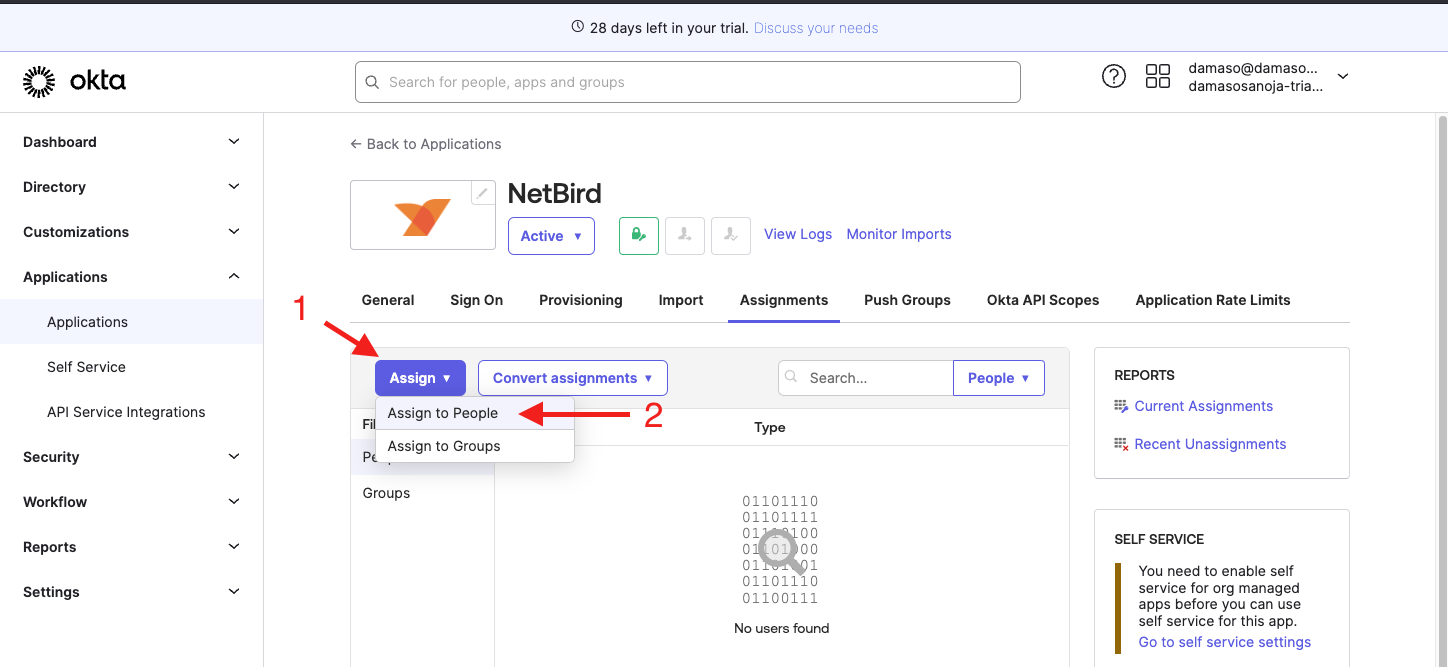
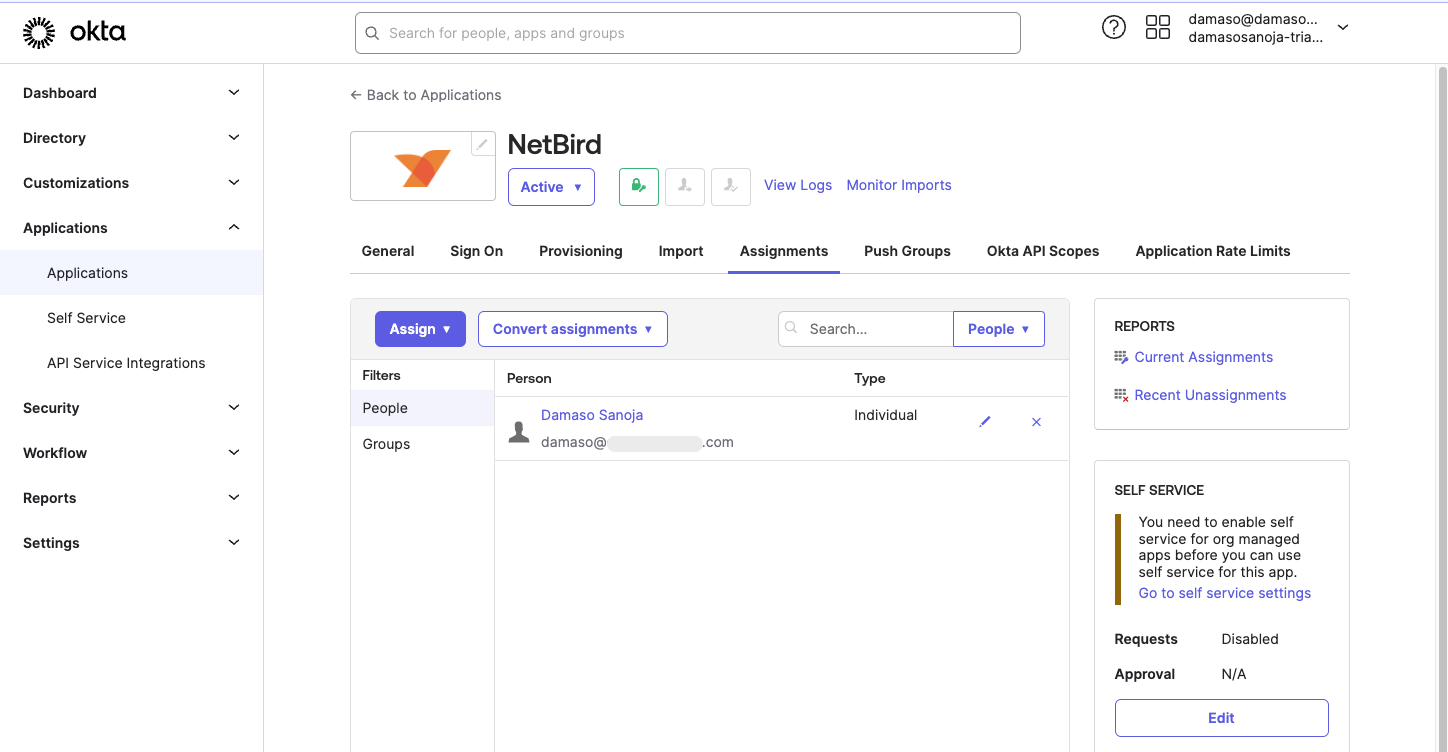
You will see a list of users. Find your user account, click Assign, and save the changes. Verify your user is assigned to the QuFabric app and click Done.
After that, you will see your user listed in the QuFabric application.
Configuring SSO in Okta
The next step is to configure Okta-QuFabric SSO integration.
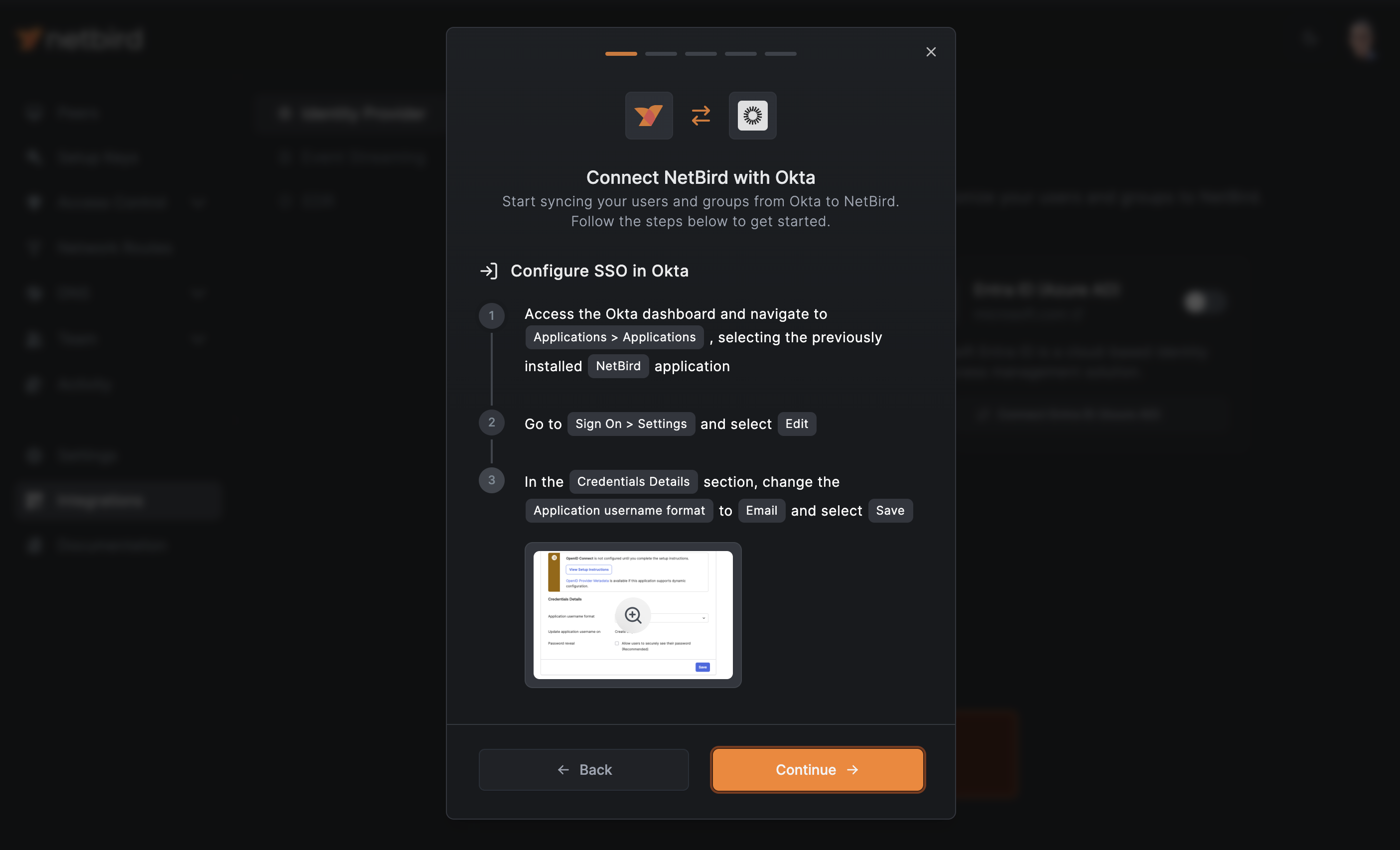
In QuFabric, click the Continue → button. A new wizard screen will appear, offering the instructions for retrieving Okta’s OpenID Connect credentials. You can click Close and navigate to Okta.
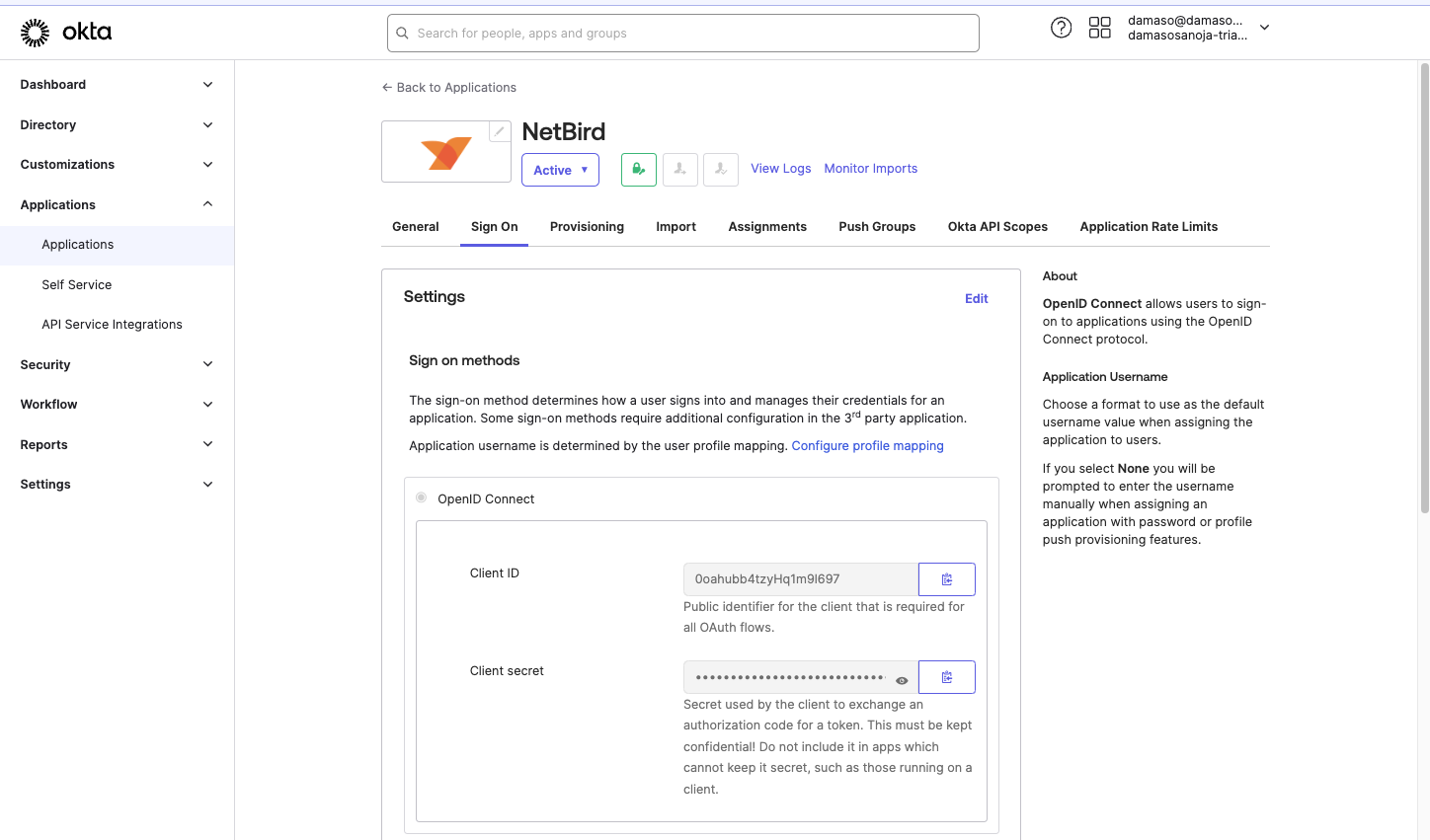
- Click on the
Sign Ontab on Okta. Look forOpenID ConnectunderSign on methodsin theSettingssection. - Copy the
Client IDvalue. - Copy the
Client Secretvalue.
Store these credentials securely, as you will need them soon.
- Click
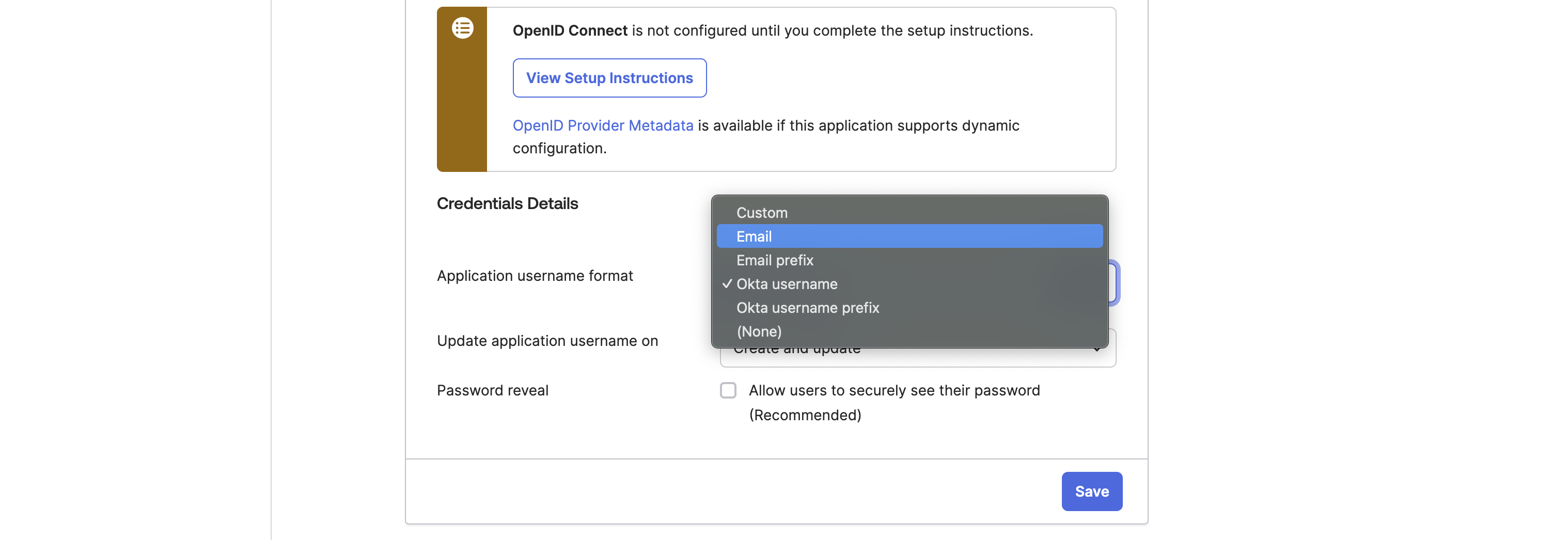
Editin theSettingssection. - In
Credential Details, change theApplication username formatfromOkta usernametoEmail. - Click the
Savebutton
- On the top right, click on your username
- Copy your Okta account domain as shown below:
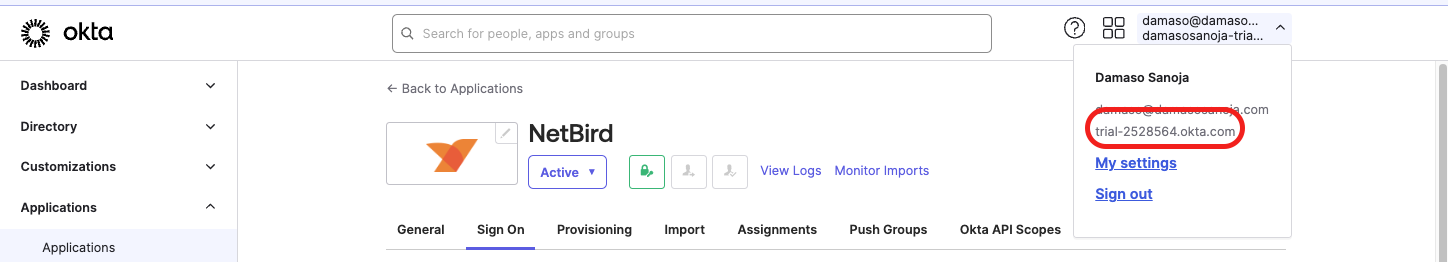
The final step is to send an email to the QuFabric team with the authentication information you just retrieved:
- Okta
Client ID - Okta
Client secret - Okta account domain
- Okta primary email domain (usually your username)
You will receive an email once the QuFabric team enables authentication for your account.
This completes the first stage, enabling Single Sign-On (SSO) from QuFabric's login page using Okta credentials. Now, you can navigate to app.qufabric.io and log in using Okta Verify.
Enabling Okta SCIM in QuFabric
In QuFabric, go to Integrations > Identity Provider and click on the Connect to Okta button.
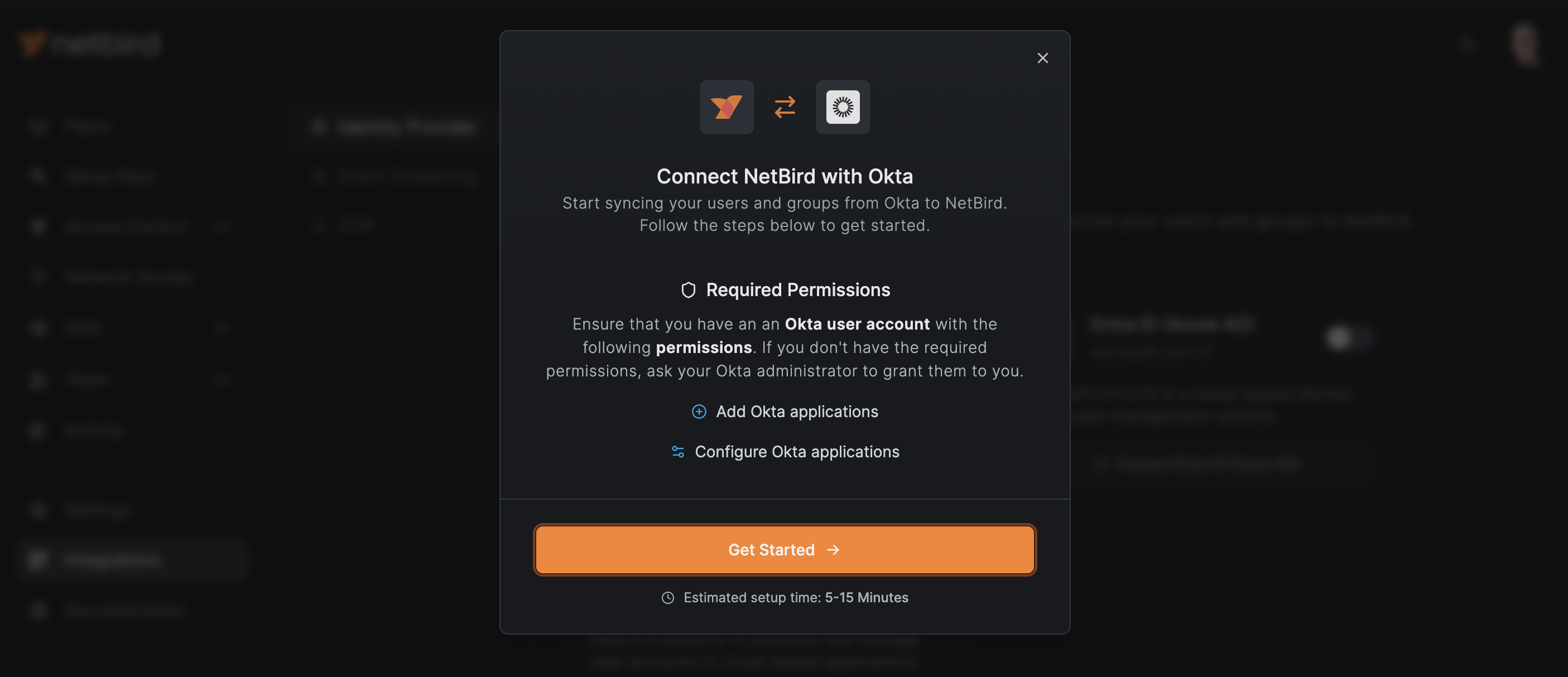
You will see a reminder of the permissions your user will require in Okta. Click the Get Started → button to continue.
If you haven't already, you'll need to set up SSO in Okta. If you've completed the previous section, skip this step and click the Continue → button.
The next screen will show you how to enable QuFabric API credentials in Okta. Copy the value of the Authorization (Bearer) token.
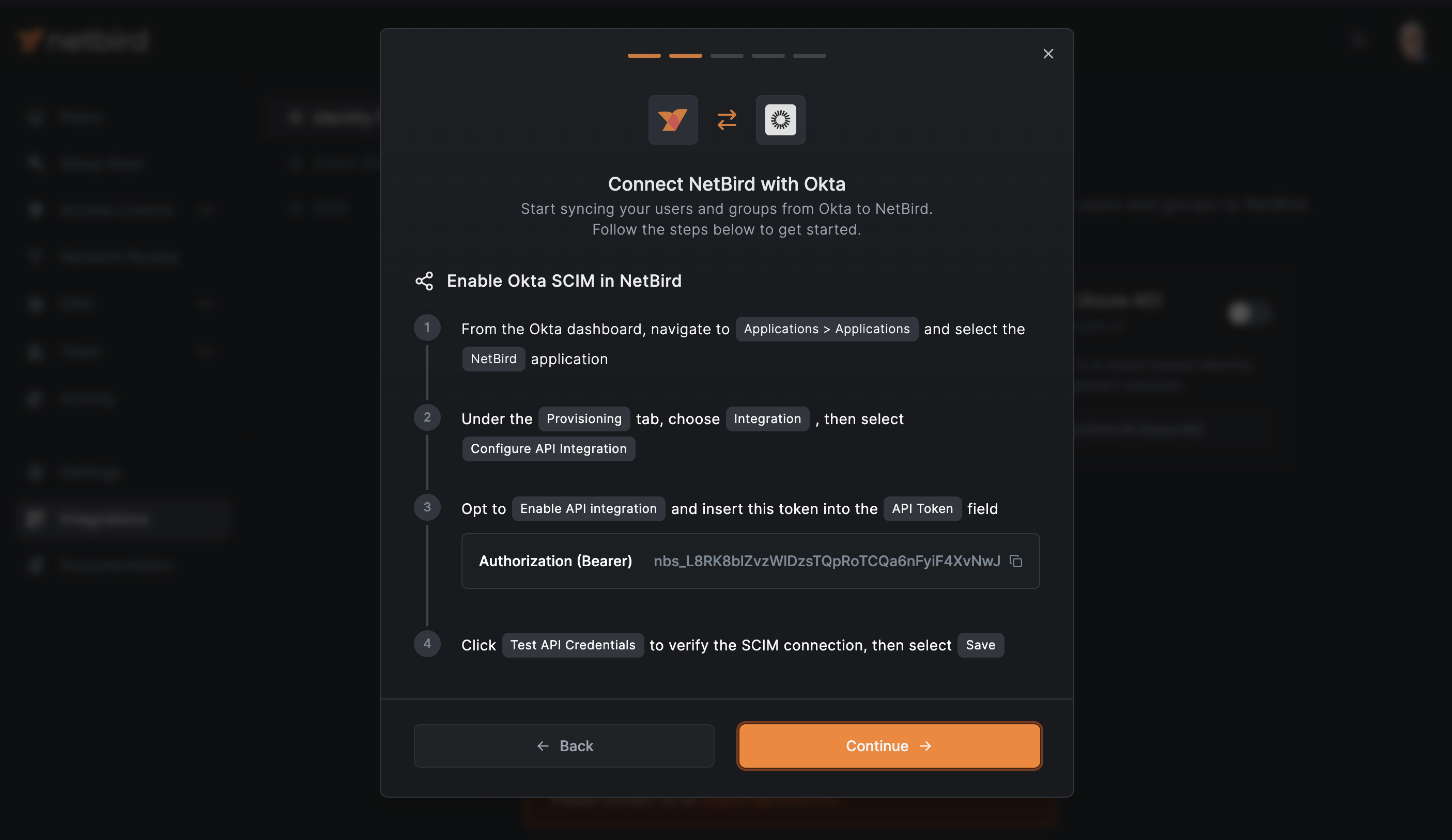
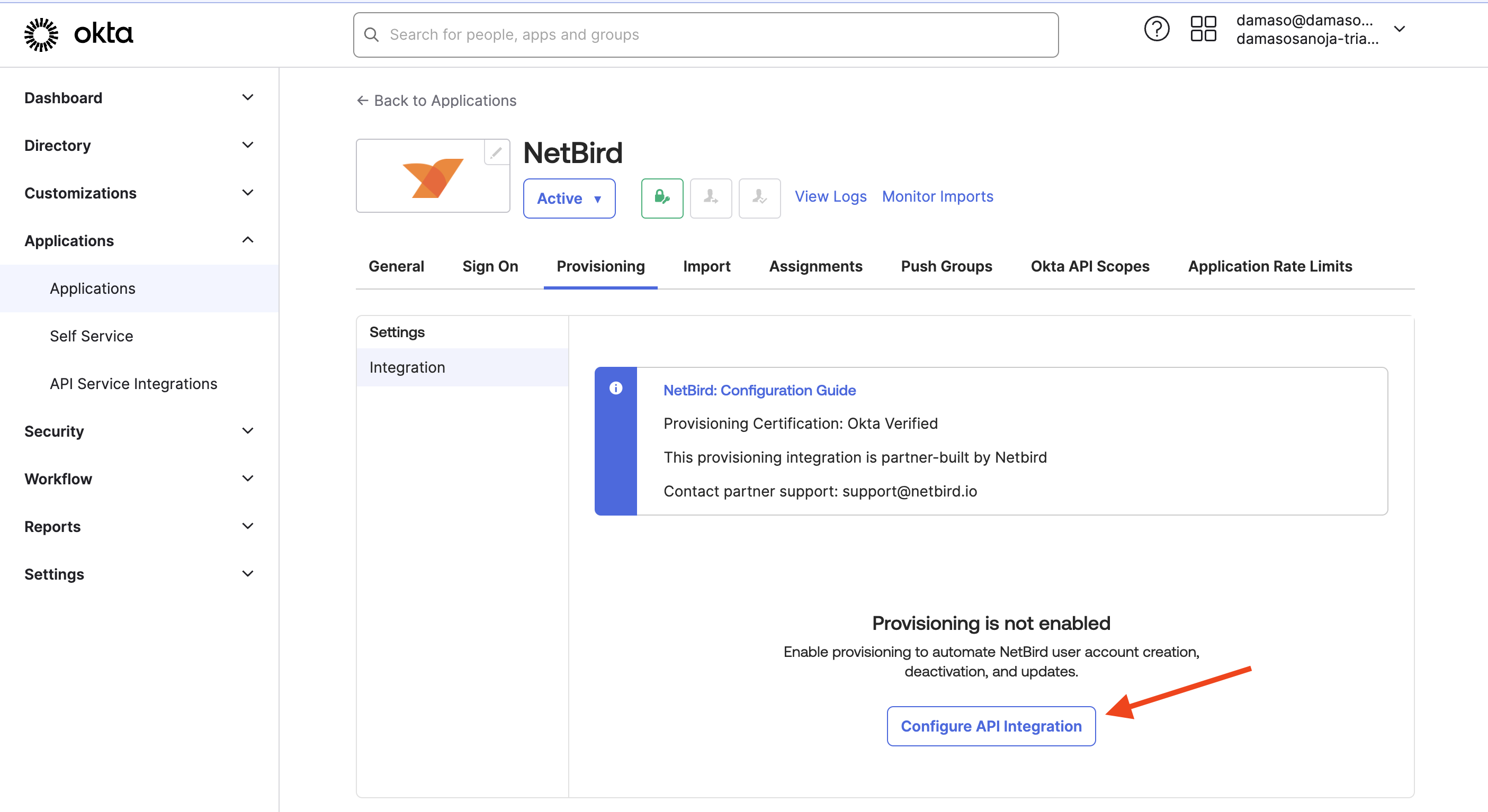
Navigate to the QuFabric app in your Okta admin dashboard. Click the Provisioning tab, then select Configure API Integration.
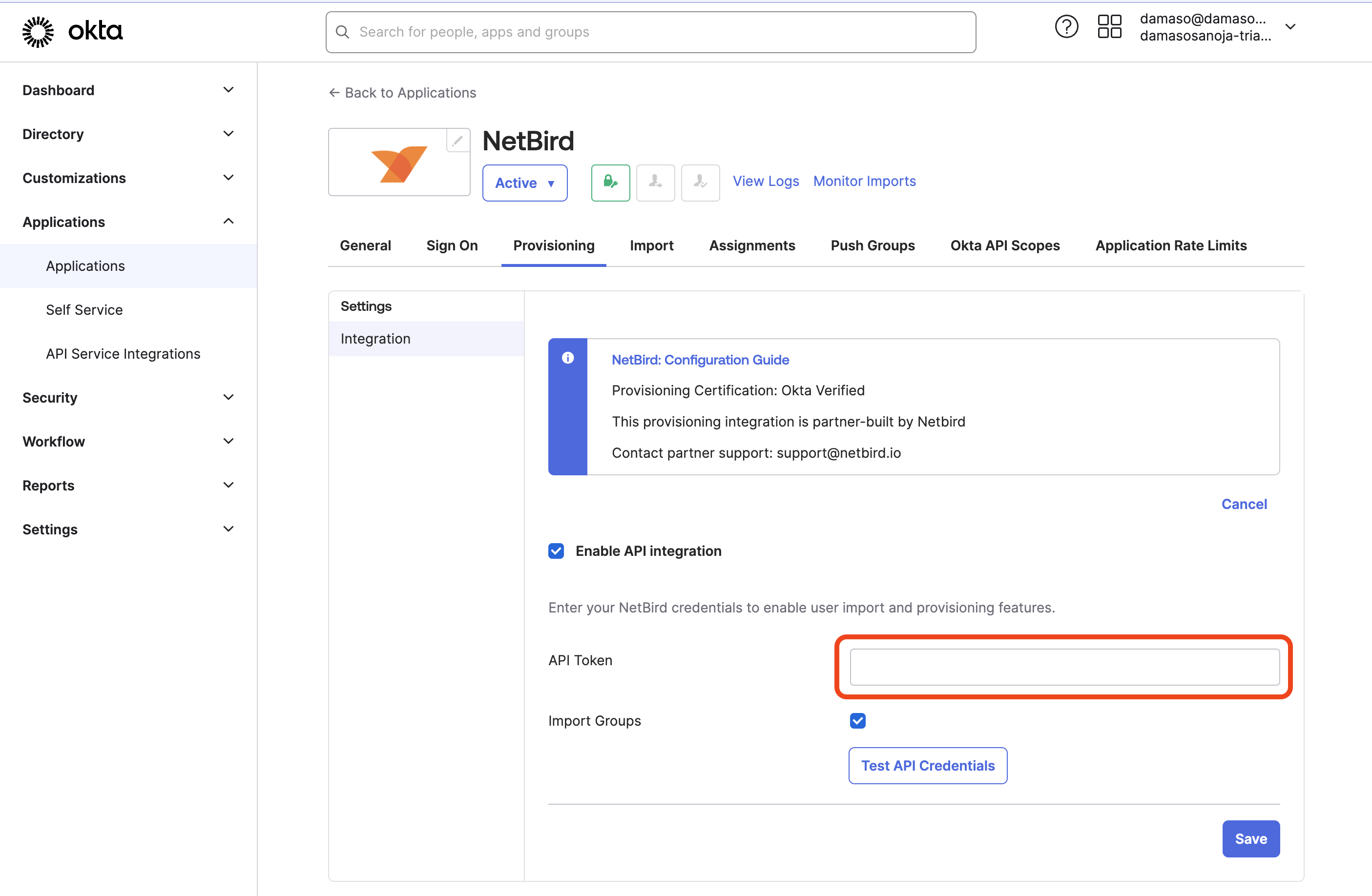
Follow these steps:
- Check the box to enable API Integration.
- Enter your QuFabric API Token.
- Click
Test API Credentialsto verify the SCIM connection.
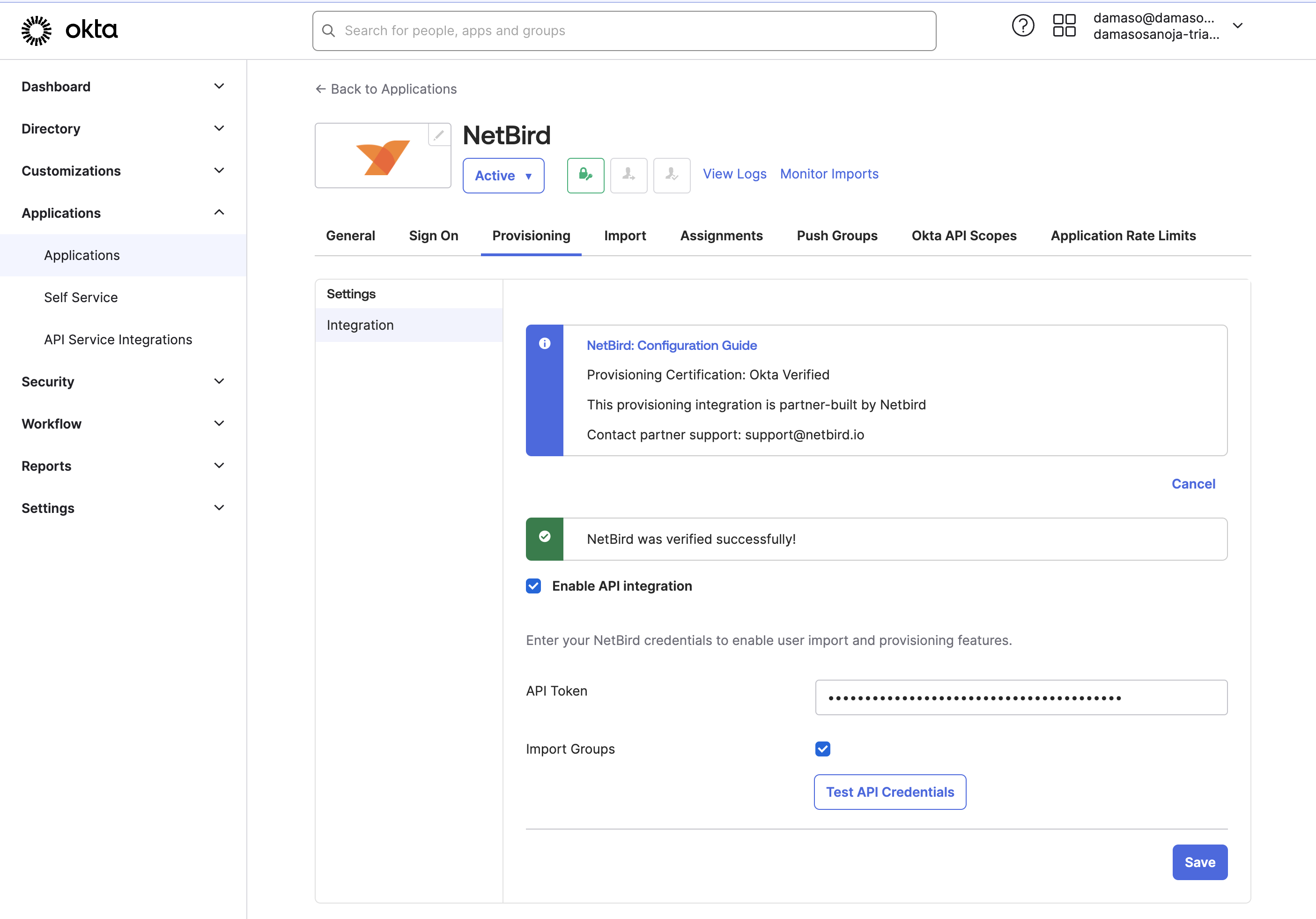
If everything works as expected, you'll see the message: "QuFabric was verified successfully!" as shown below. Click Save to continue.
Configuring SCIM Provisioning to QuFabric
On QuFabric, click Continue →. You'll see instructions for configuring SCIM provisioning to QuFabric.
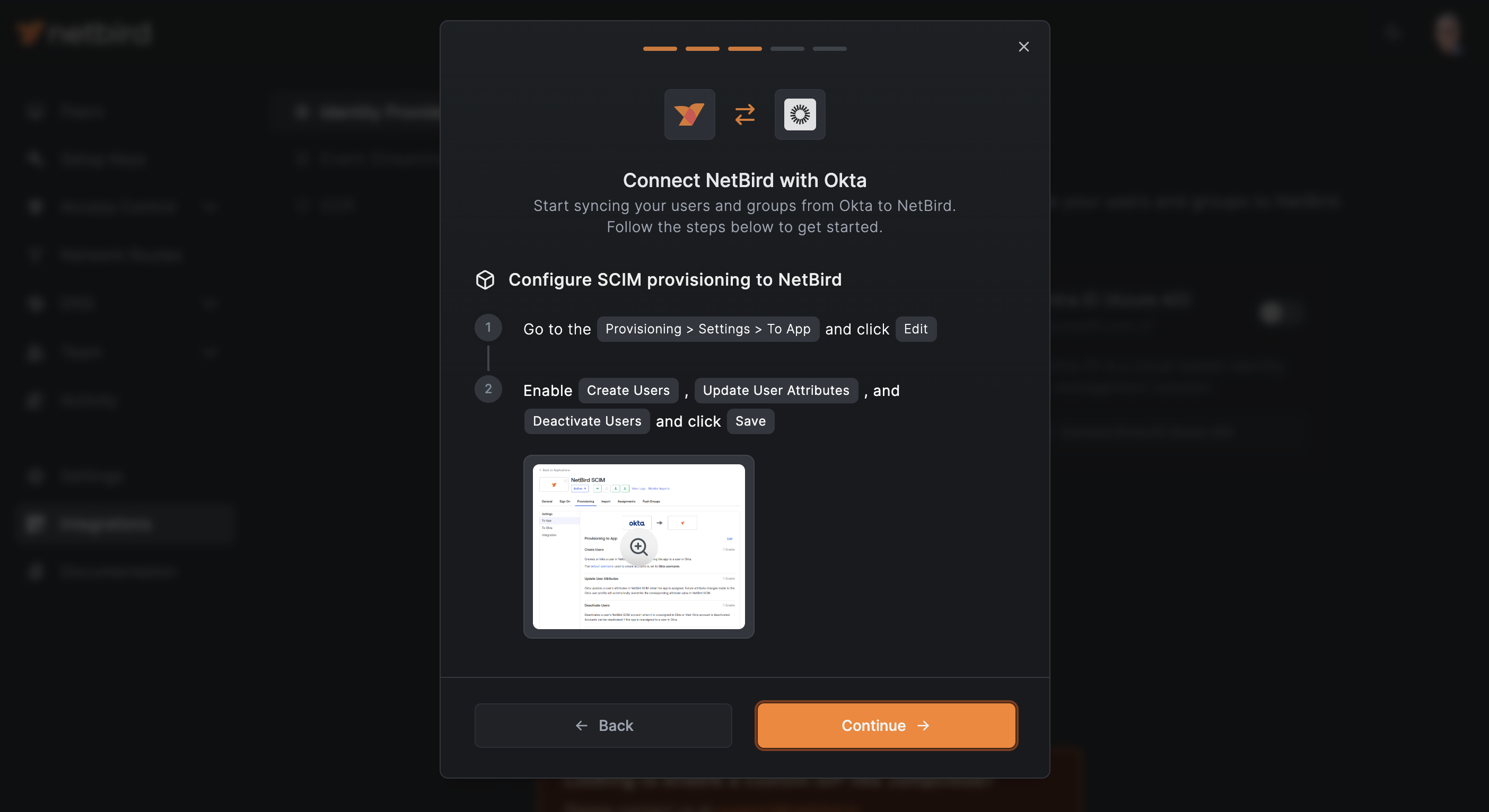
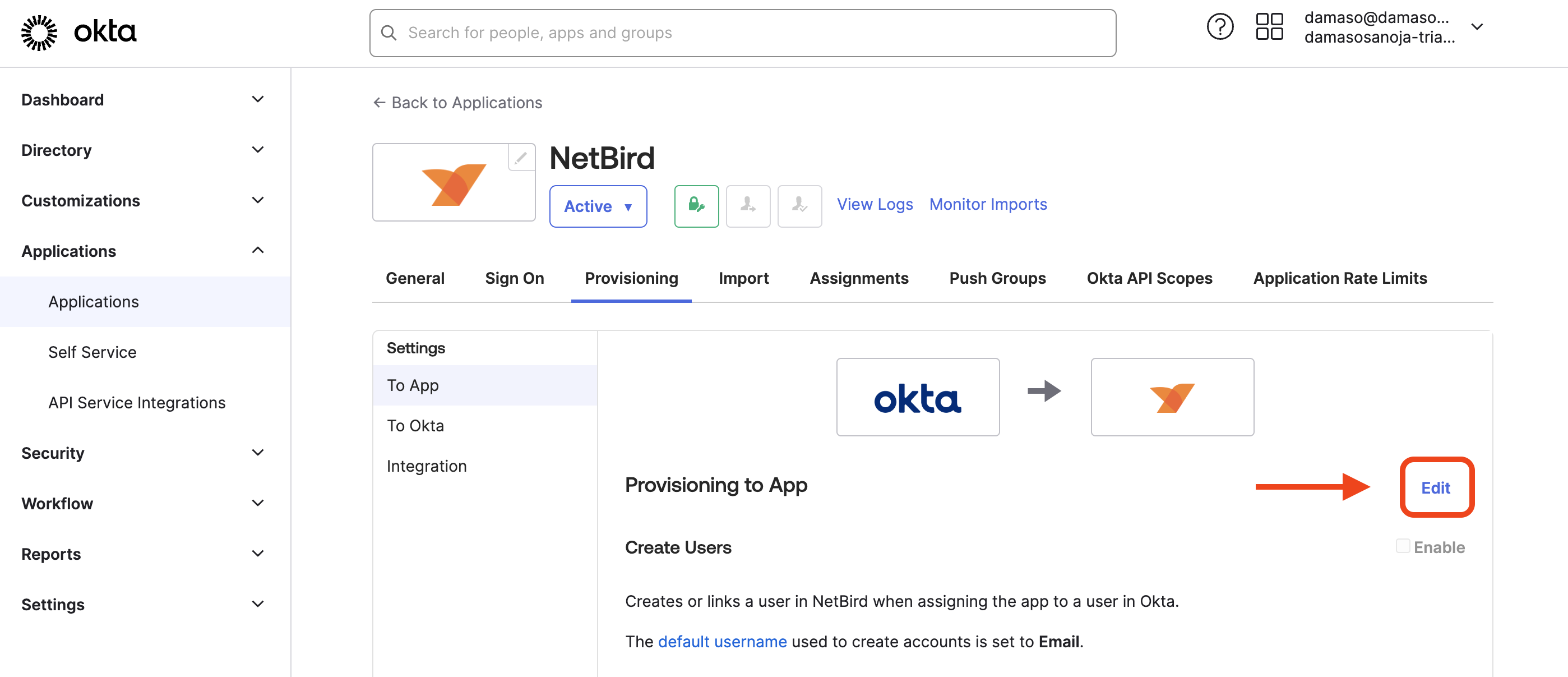
Back to Okta, click Edit as shown below.
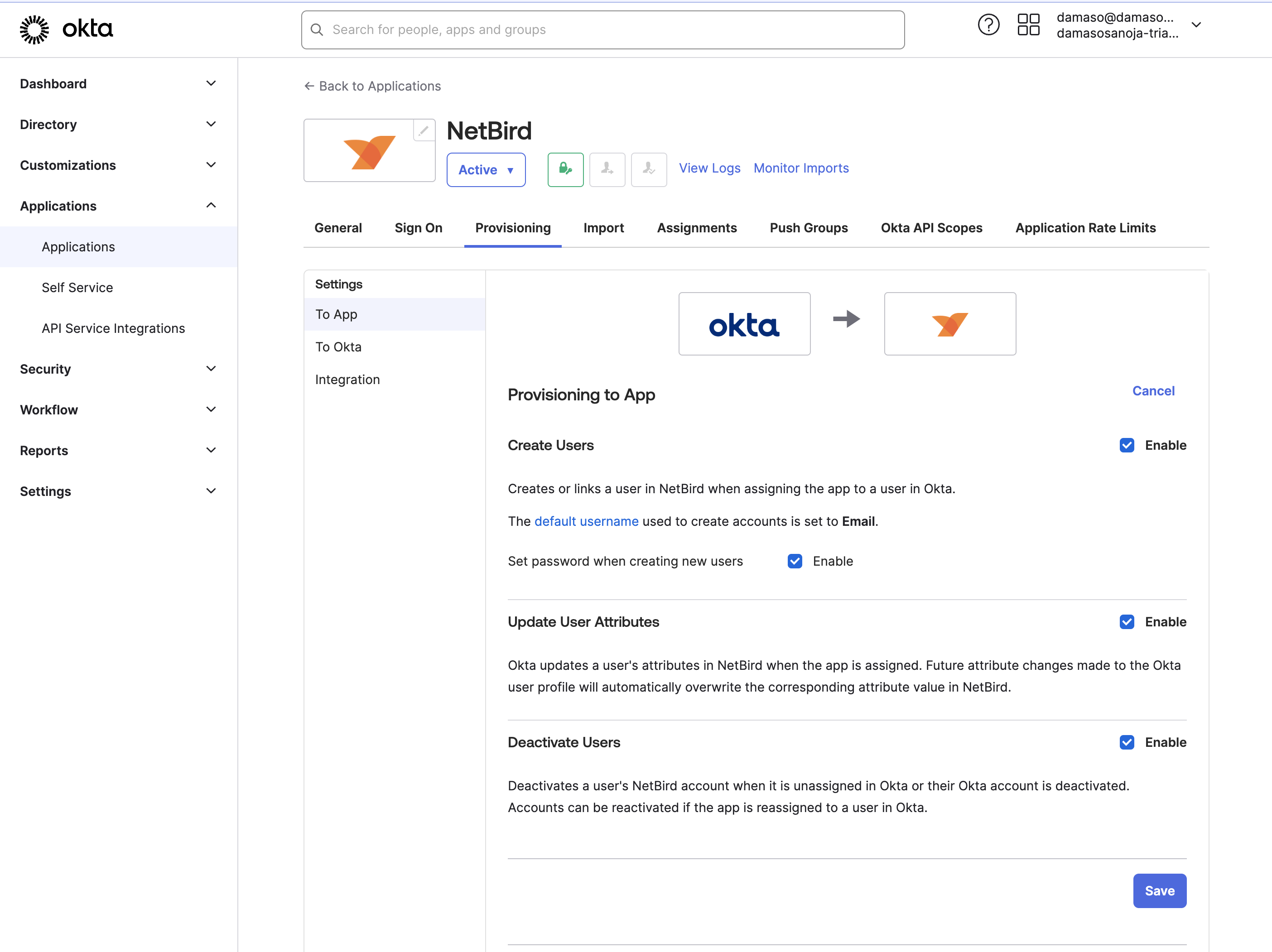
Enable Okta to create, update, and deactivate QuFabric users by checking the corresponding boxes:
- Create Users
- Update User Attributes
- Deactivate Users
When done, click Save.
Assigning QuFabric Application to Okta Groups
In QuFabric, click Continue →, you'll see the steps for assigning the QuFabric integration to Okta groups.

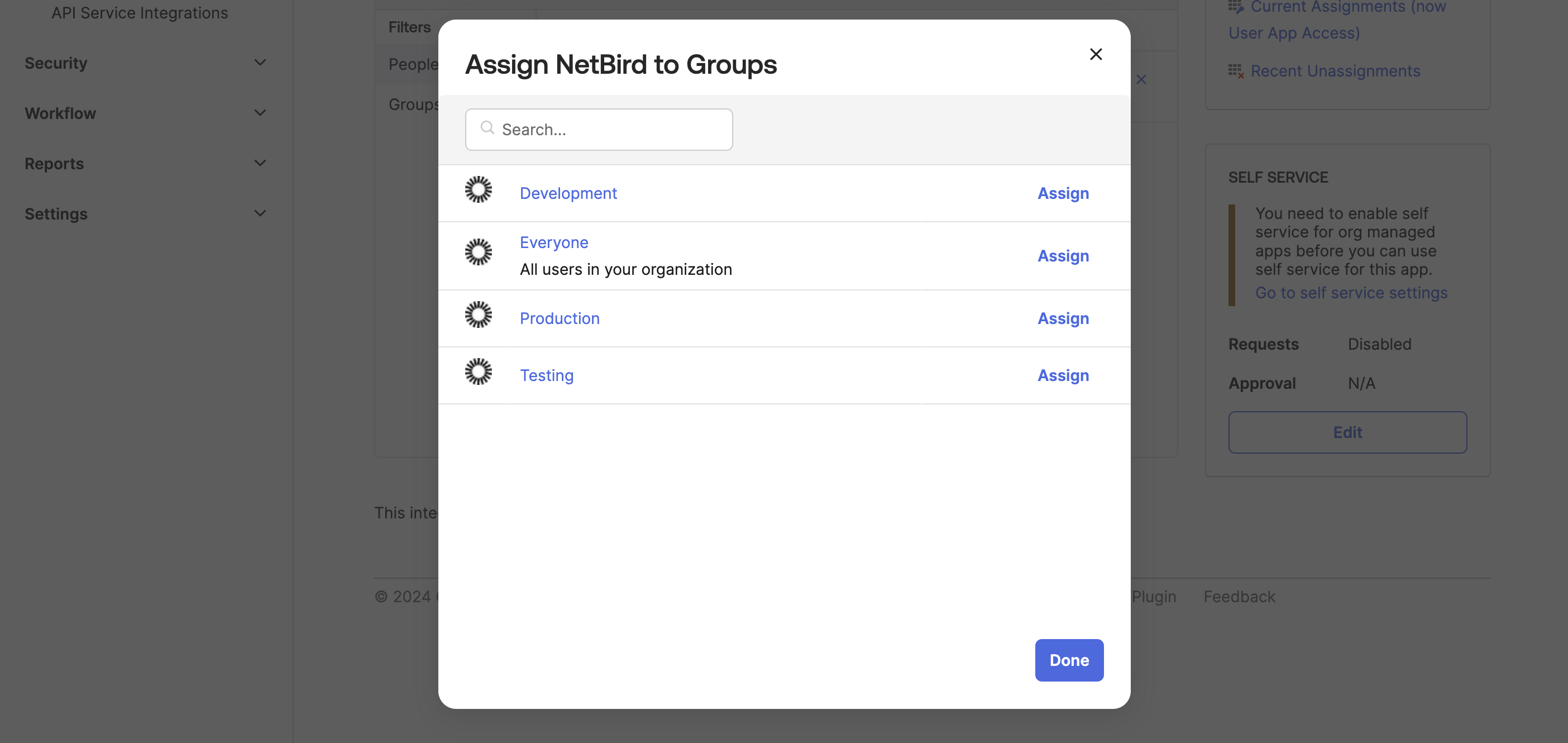
- Navigate to the
Assignmentstab. - Similar than before when you assigned your user to QuFabric app, click the
Assignbutton - This time, select
Assign to Groups. - Select Okta groups that you want to assign to the QuFabric app.
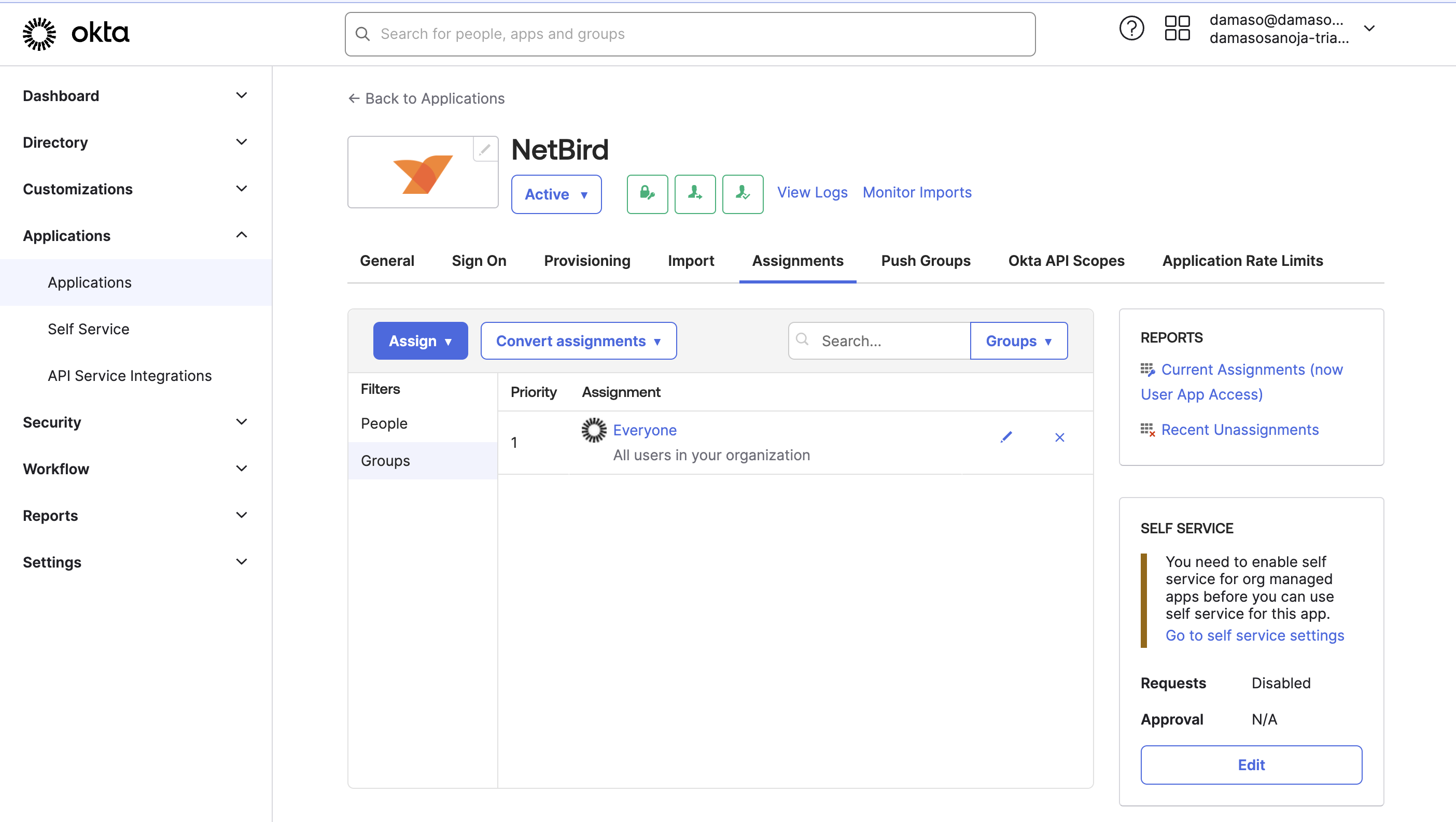
Once you assign the desired groups, click Done. You'll see the selected groups listed in Okta.
Push Okta Groups to QuFabric
One more time, go to QuFabric and click Continue →. You'll see the final instructions to push Okta groups to QuFabric.
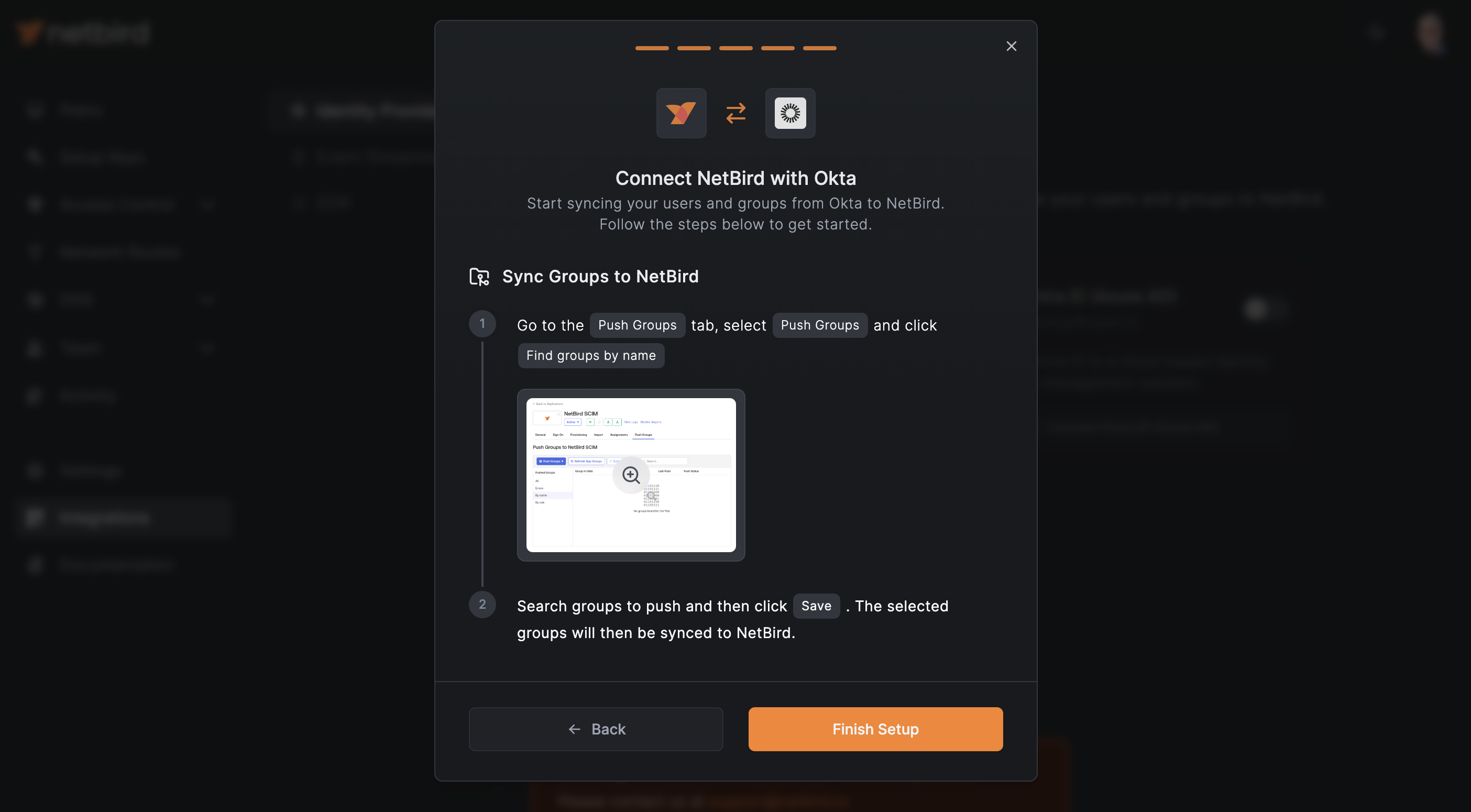
- In Okta, navigate to
Push Groupstab - Click the
Push Groupsbutton - Select
Find groups by name - Search for specific groups to push to QuFabric.

Once you finish, go back to QuFabric and click Finish Setup. You can verify the synchronization by navigating to Team > Users
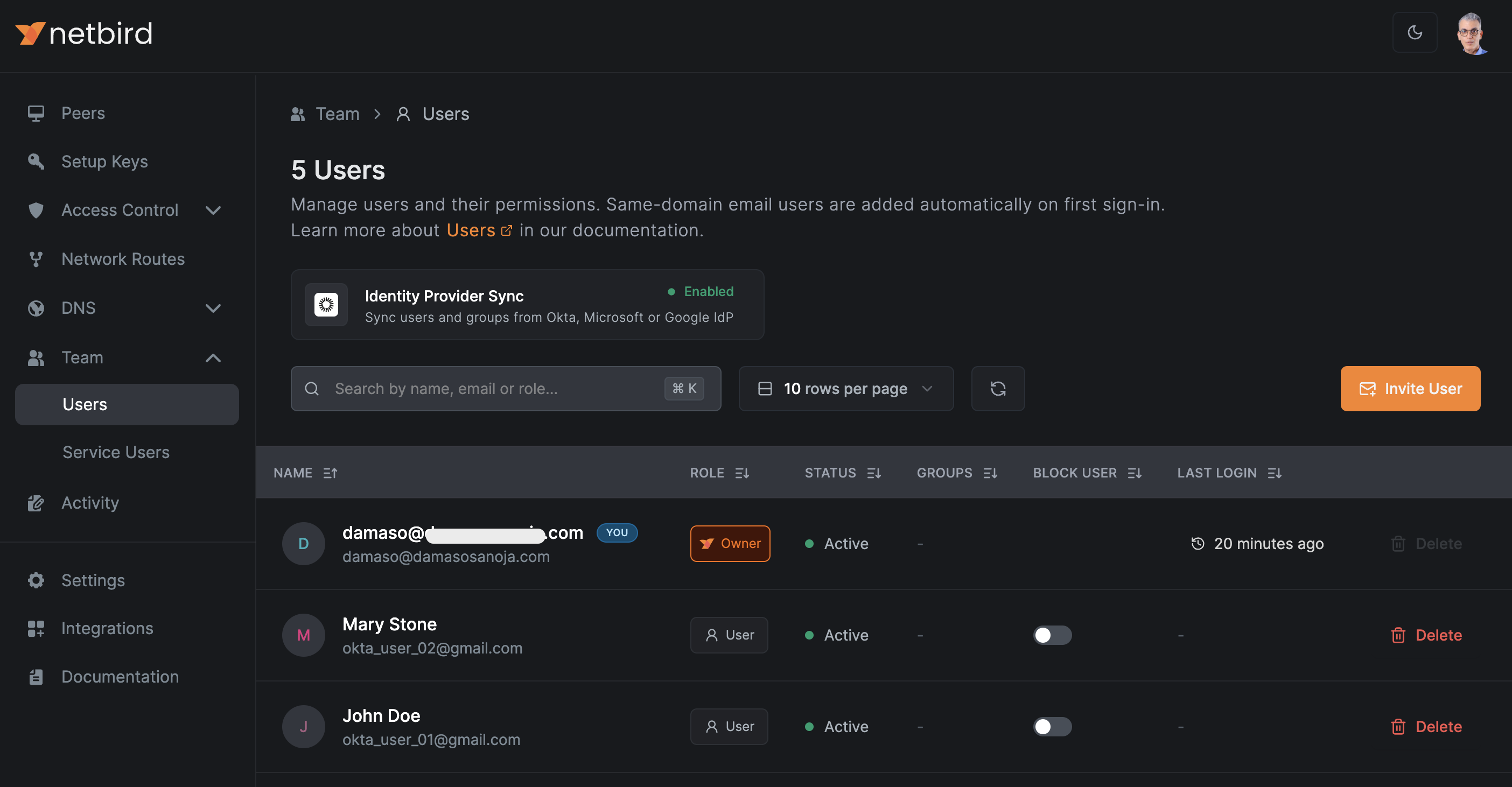
The users listed in QuFabric should match those you created in Okta.

SCIM provisioning will manage only resources that are created through Okta. Any resources created directly in QuFabric will not be managed by SCIM.
Synced groups will only be available for membership and will not change the role of user in QuFabric

