Zitadel SSO with QuFabric Self-Hosted (Advanced)
Zitadel is an open-source identity infrastructure platform designed for cloud-native environments. It provides multi-tenancy, customizable branding, passwordless authentication, and supports protocols like OpenID Connect, OAuth2, SAML2, and LDAP.
Zitadel was previously used in the QuFabric quickstart script. If you have an existing Zitadel deployment, you can continue using it as a standalone IdP or migrate to the embedded IdP with Zitadel as an external IdP directly in the QuFabric Management Dashboard.
Standalone Setup (Advanced)
QuFabric includes built-in local user management powered by an embedded IdP, allowing you to create and manage users directly without requiring an external identity provider. You can also add multiple external identity providers alongside local users, giving users multiple login options.
We highly recommend using the simpler setup that adds Zitadel as an external IdP directly in the QuFabric Management Dashboard. This approach requires minimal configuration, works alongside local users, and doesn't require replacing your embedded IdP. See the Management Setup (Recommended) section in the main Zitadel documentation.
The standalone setup below replaces your embedded IdP entirely and is only recommended for experienced Zitadel administrators who need full control over authentication and user management.
Use Zitadel as your primary identity provider instead of QuFabric's embedded IdP. This option gives you full control over authentication and user management, is recommended for experienced Zitadel administrators as it also requires additional setup and ongoing maintenance.
For most deployments, the embedded IdP is the simpler choice — it's built into QuFabric, fully integrated, and requires minimal configuration to get started. For this implementation, go back up to the Management Setup (Recommended) section above.
If you prefer not to self-host, Zitadel offers a managed cloud option at zitadel.com.
Prerequisites
- Zitadel instance (cloud or self-hosted) with SSL
- Docker and Docker Compose for QuFabric
Step 1: Create and Configure Zitadel Application
- Navigate to Zitadel console
- Click Projects at the top menu, then click Create New Project
- Fill in:
- Name:
NETBIRD
- Name:
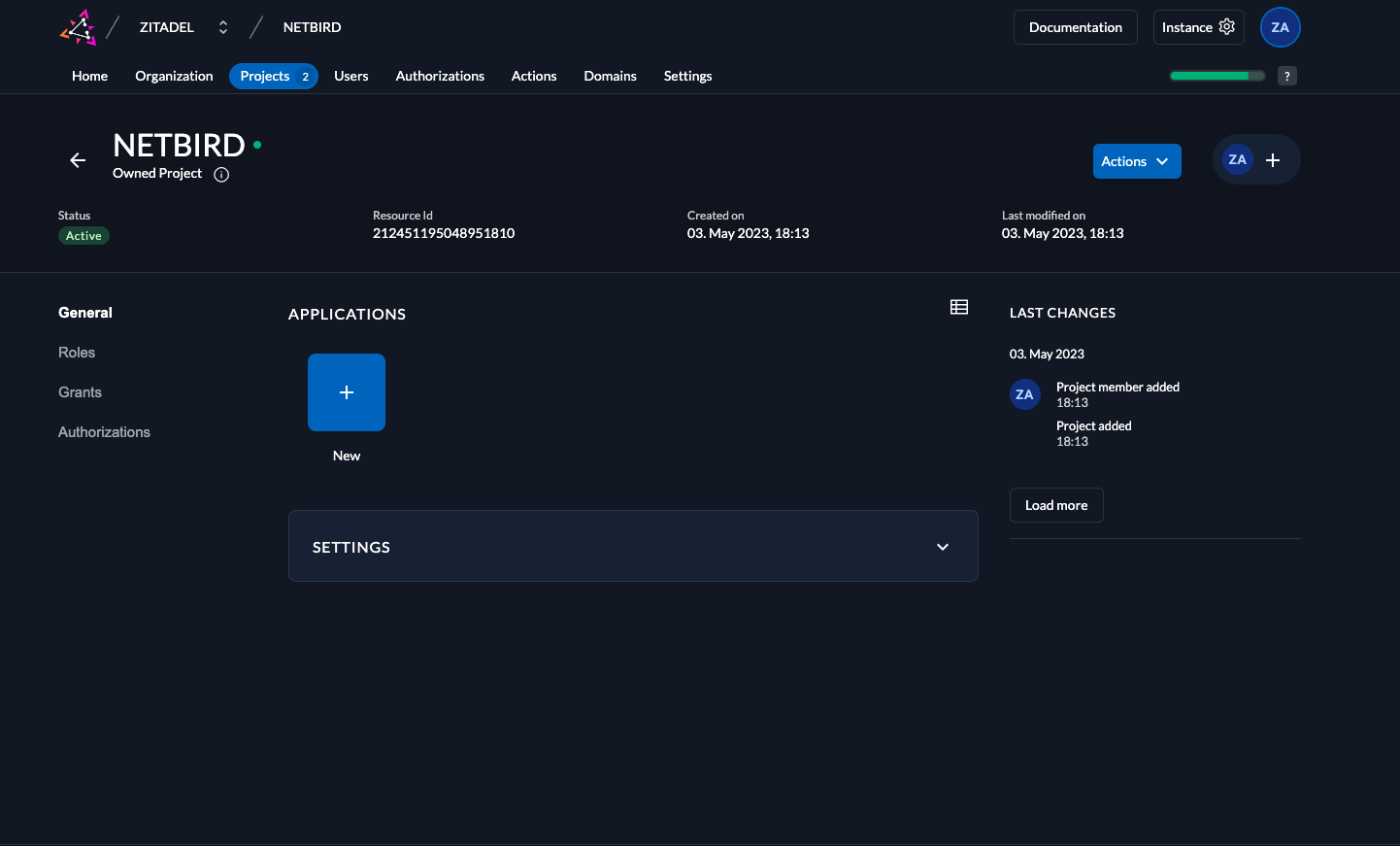
- Click Projects and select NETBIRD project
- Click New in Applications section
- Fill in:
- Name:
qufabric - Type of Application:
User Agent
- Name:
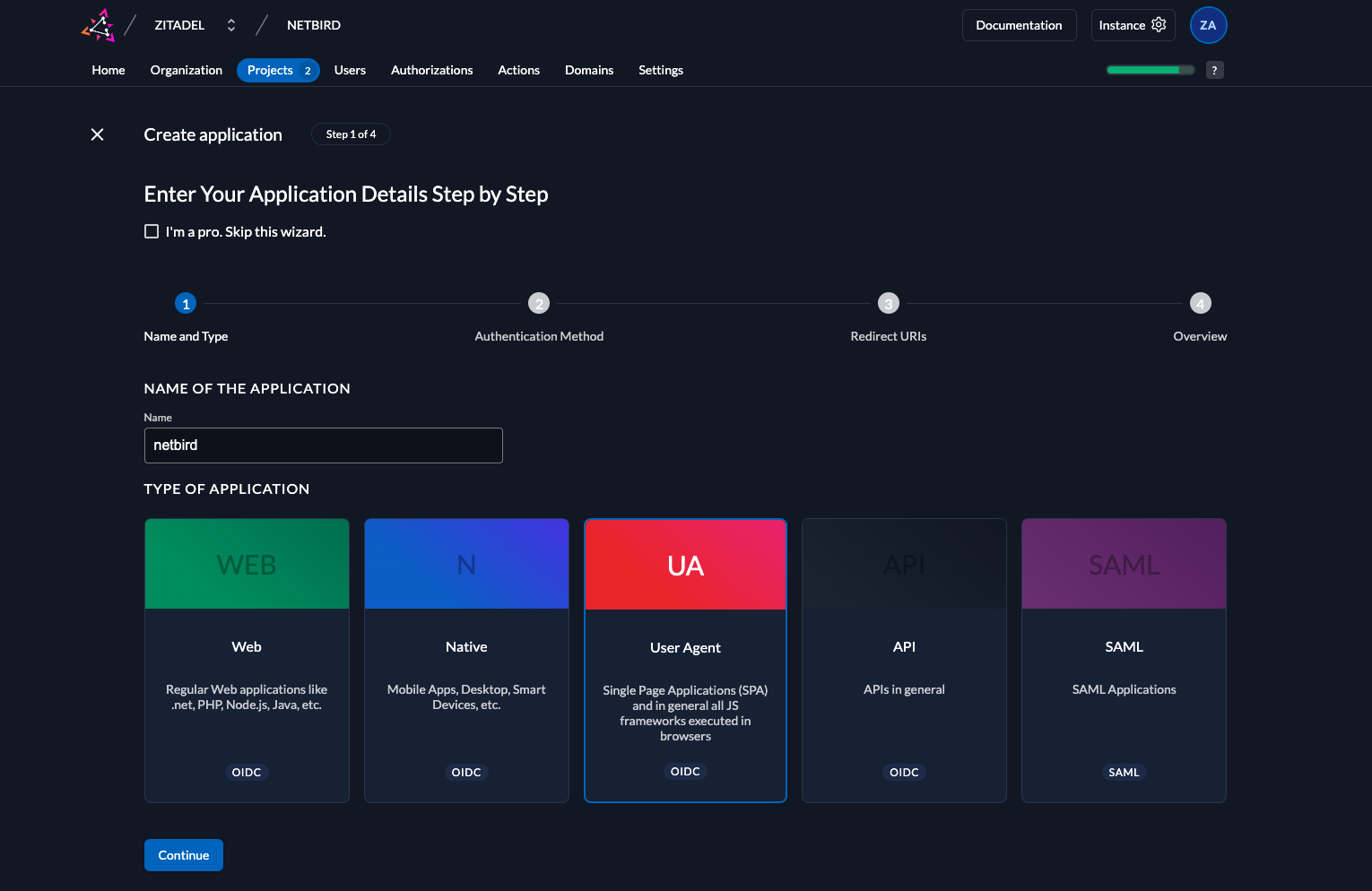
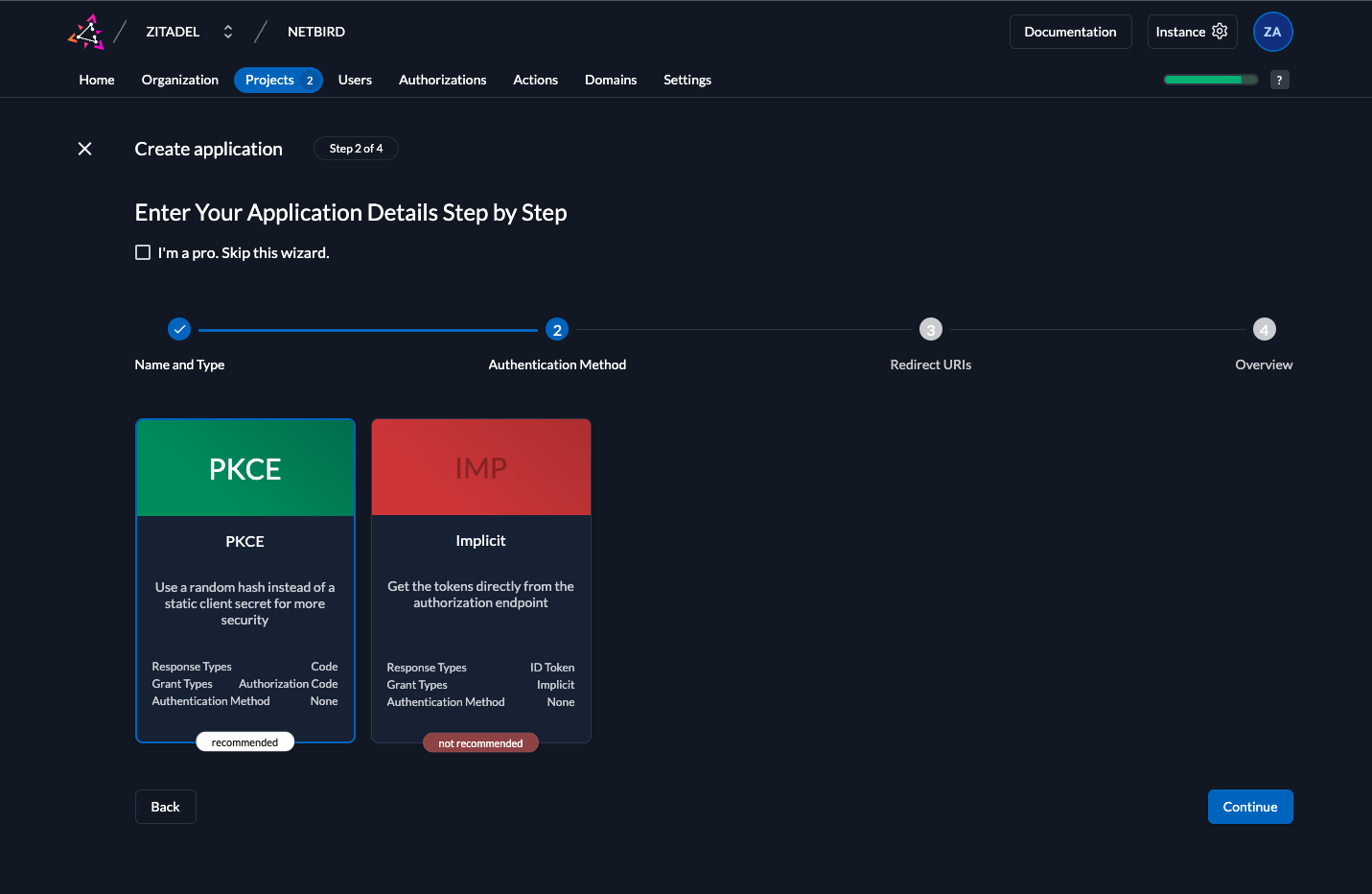
- Click Continue and set:
- Authentication Method:
PKCE
- Authentication Method:
- Click Continue and configure:
- Redirect URIs:
https://<domain>/authhttps://<domain>/silent-authhttp://localhost:53000
- Post Logout URIs:
https://<domain>/
- Redirect URIs:
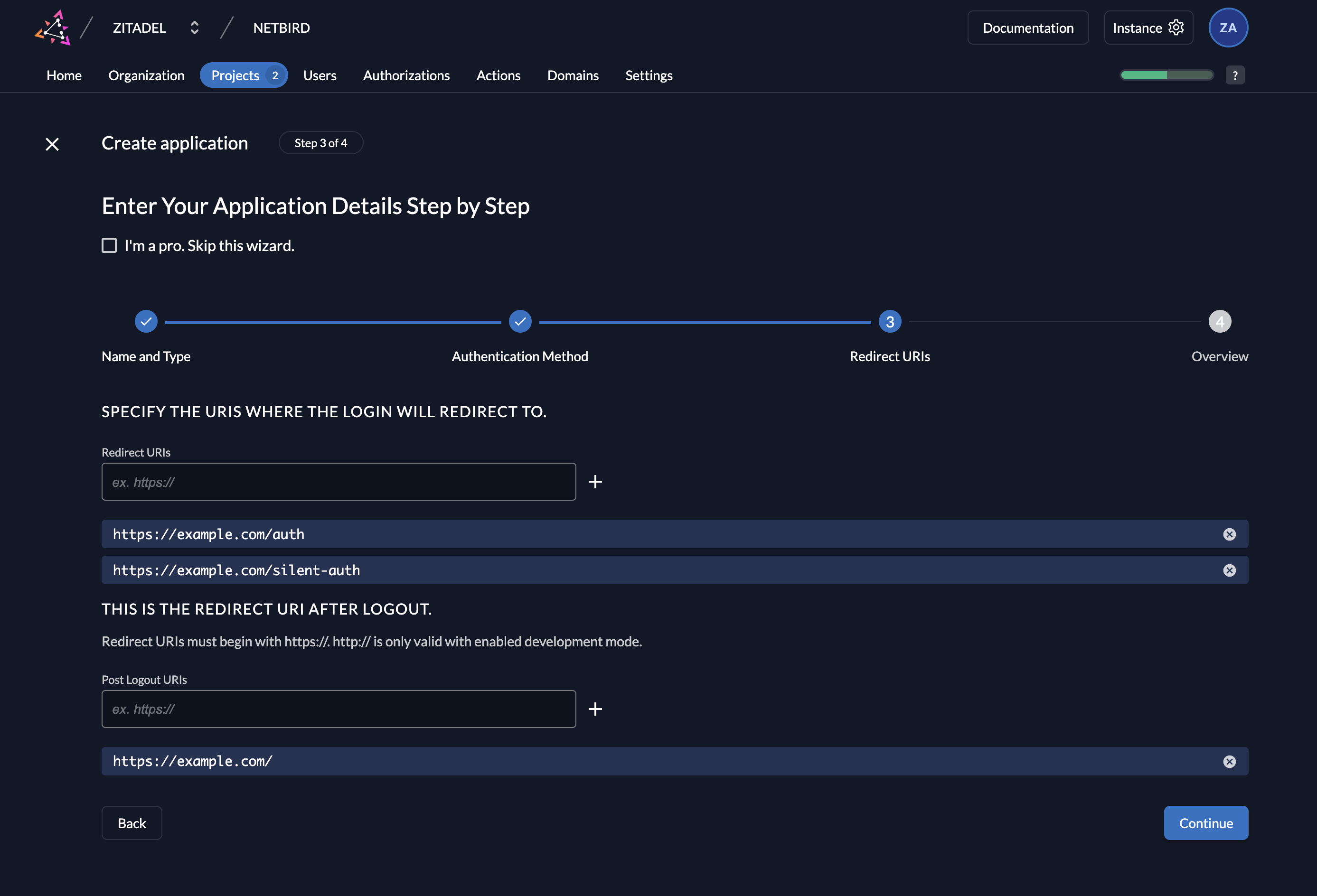
- Click Create and then Close
- Under Grant Types, select
Authorization Code,Device Code, andRefresh Token - Click Save
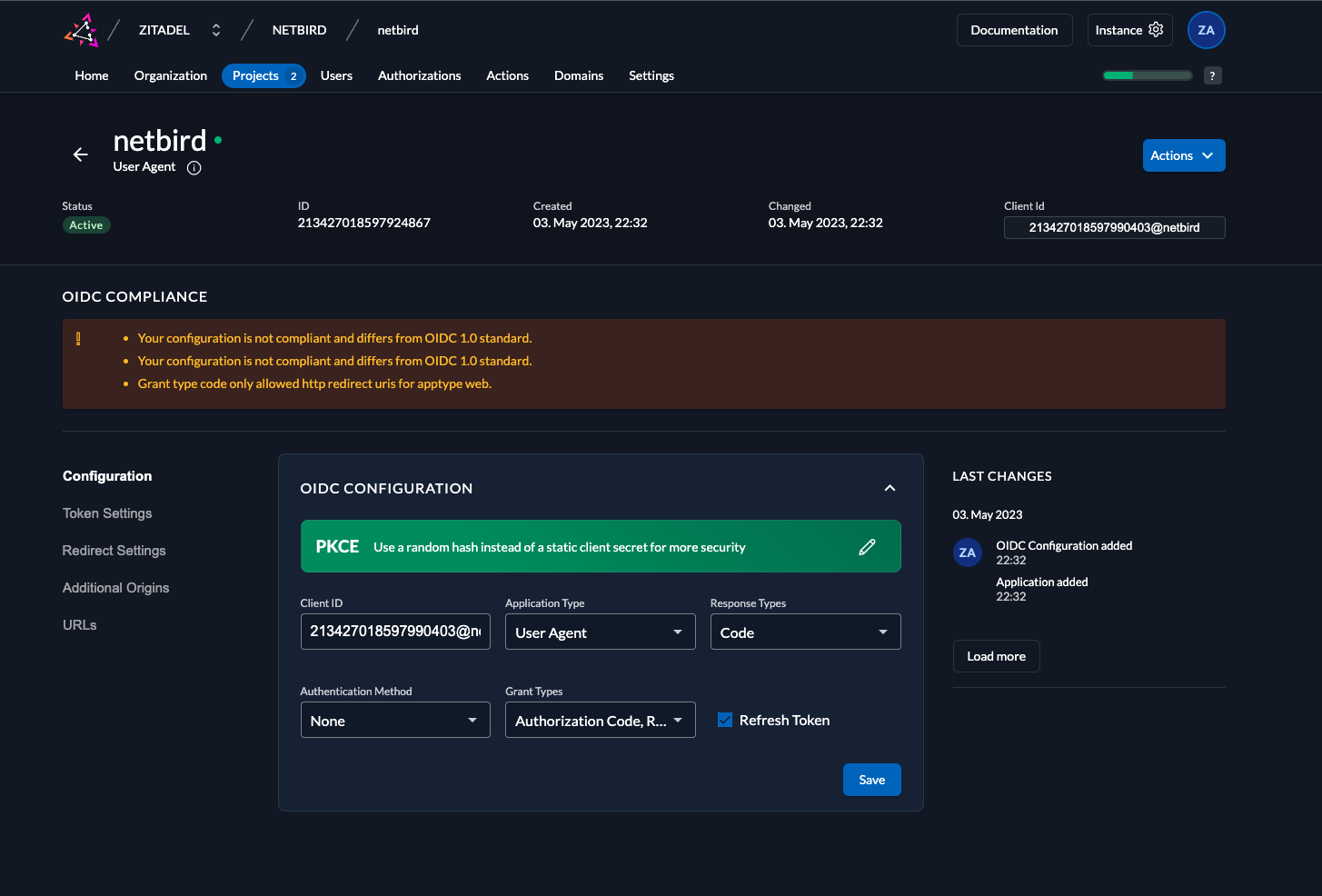
- Copy Client ID for later use
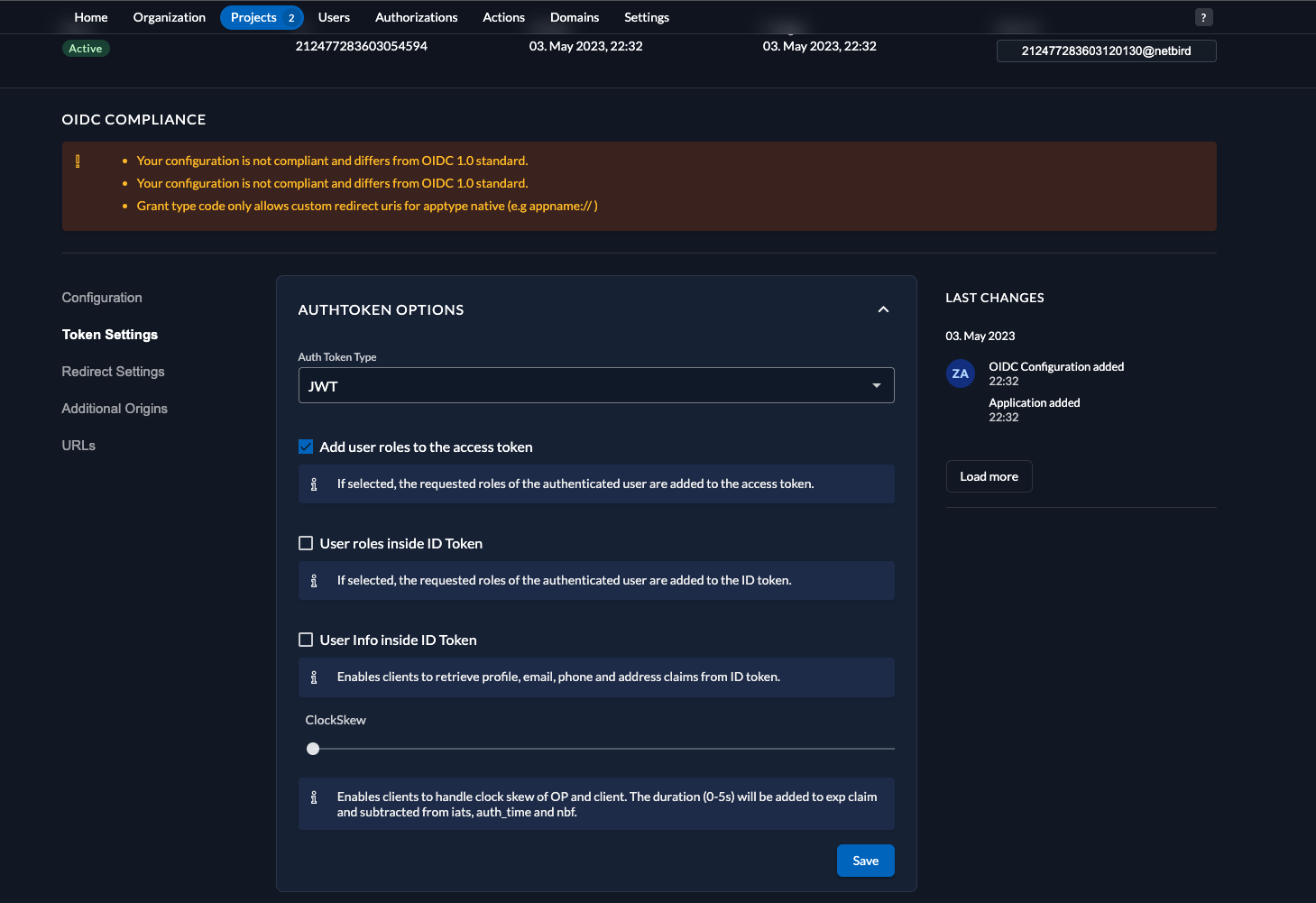
Step 2: Configure Token Settings
- Select the qufabric application
- Click Token Settings in the left menu
- Configure:
- Auth Token Type:
JWT - Check Add user roles to the access token
- Auth Token Type:
- Click Save
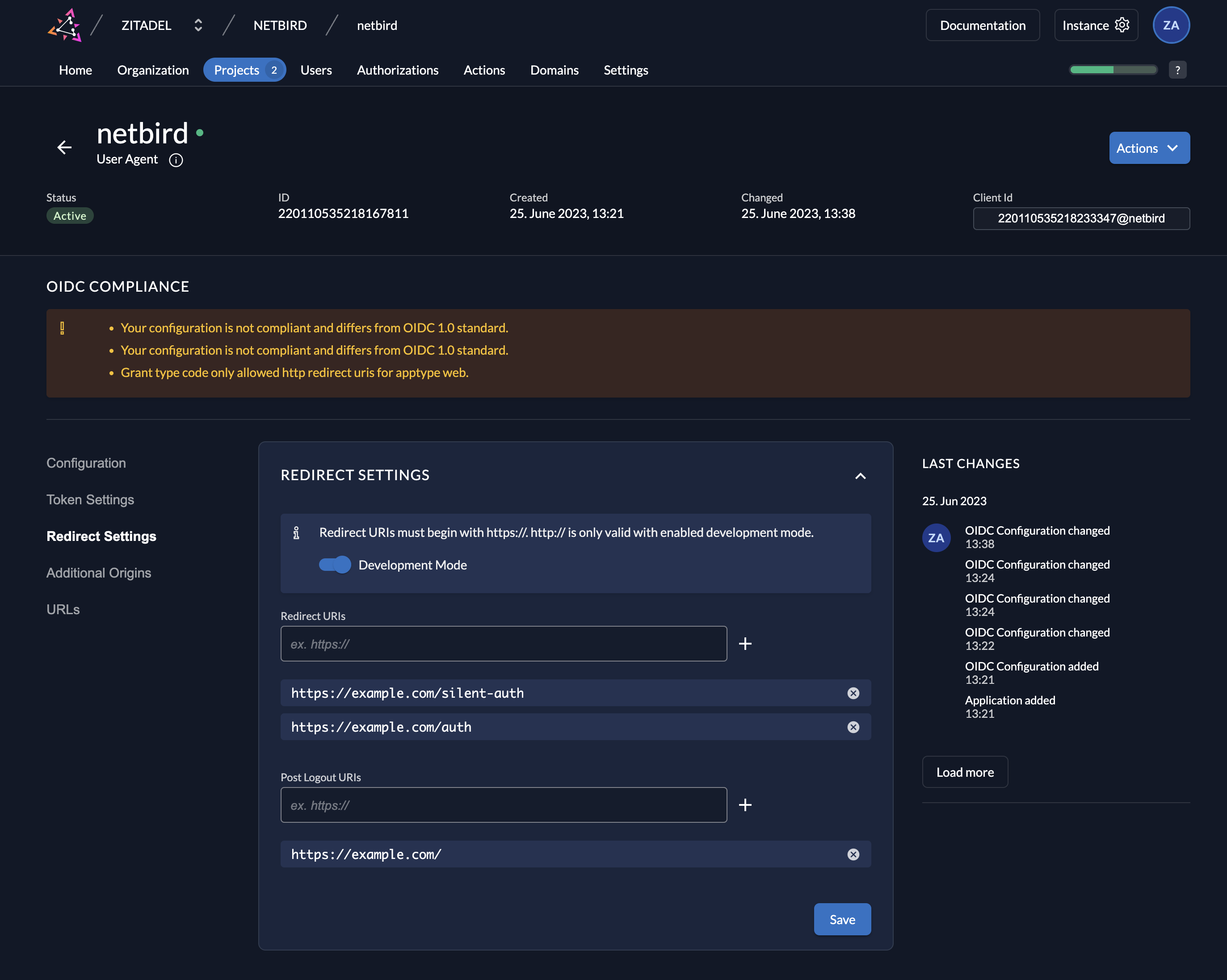
Step 3: Configure Redirect Settings (Development Only)
This step is only for development mode without SSL.
- Click Redirect Settings in the left menu
- Toggle Development Mode
- Click Save
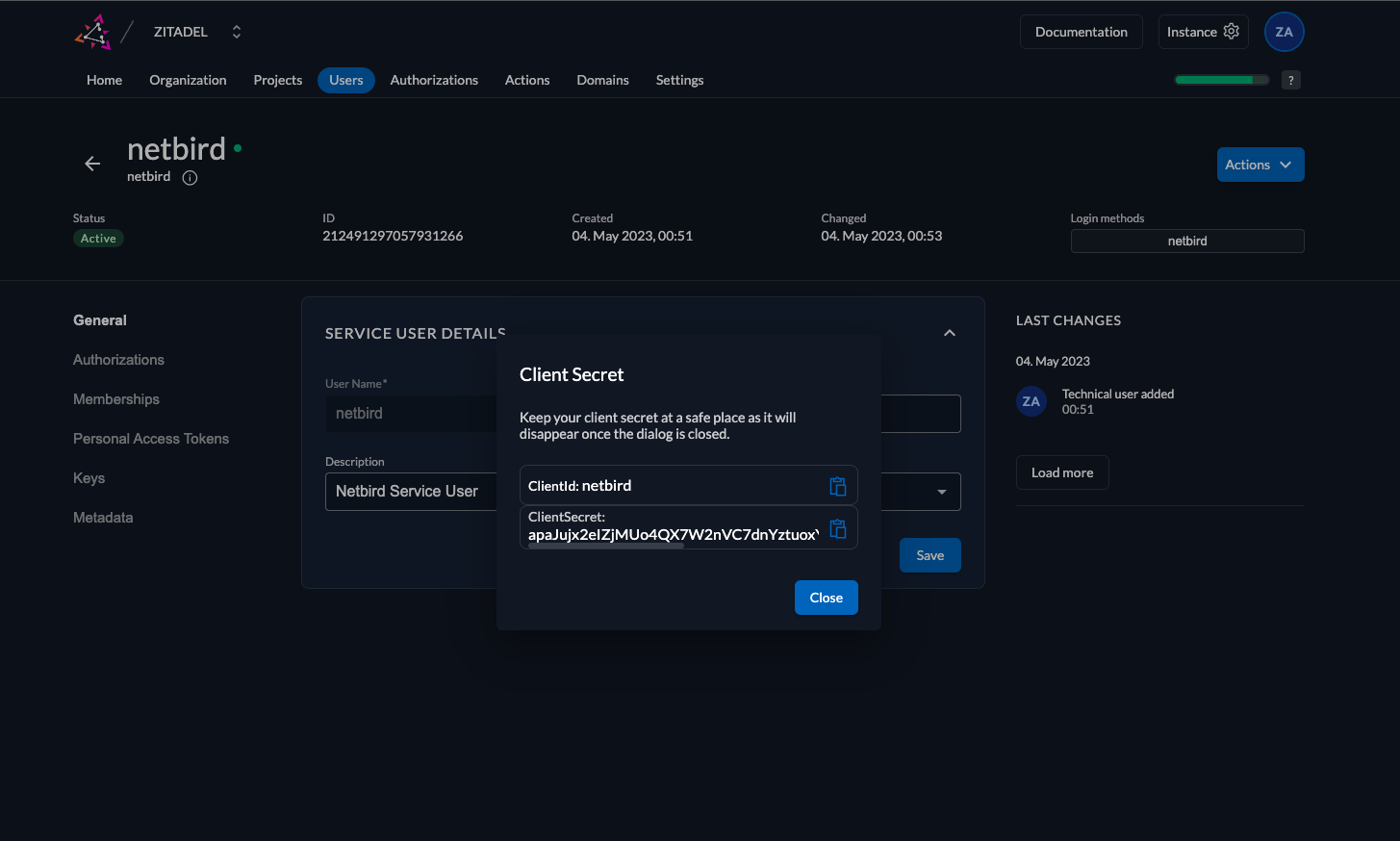
Step 4: Create Service User
- Click Users in the top menu
- Select Service Users tab
- Click New
- Fill in:
- User Name:
qufabric - Name:
qufabric - Description:
QuFabric Service User - Access Token Type:
JWT
- User Name:
- Click Create
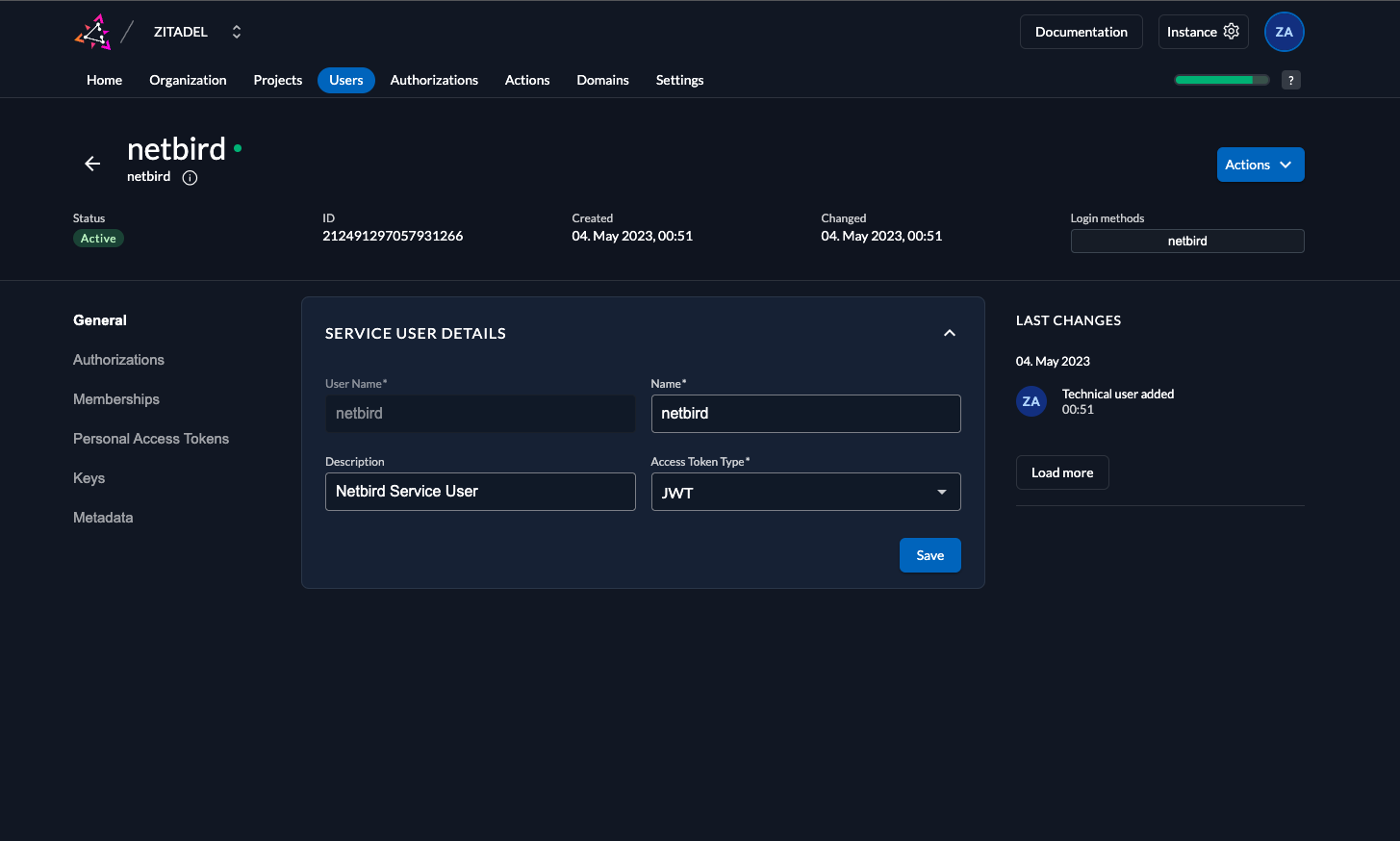
- Click Actions in the top right corner
- Click Generate Client Secret
- Copy ClientSecret for later use
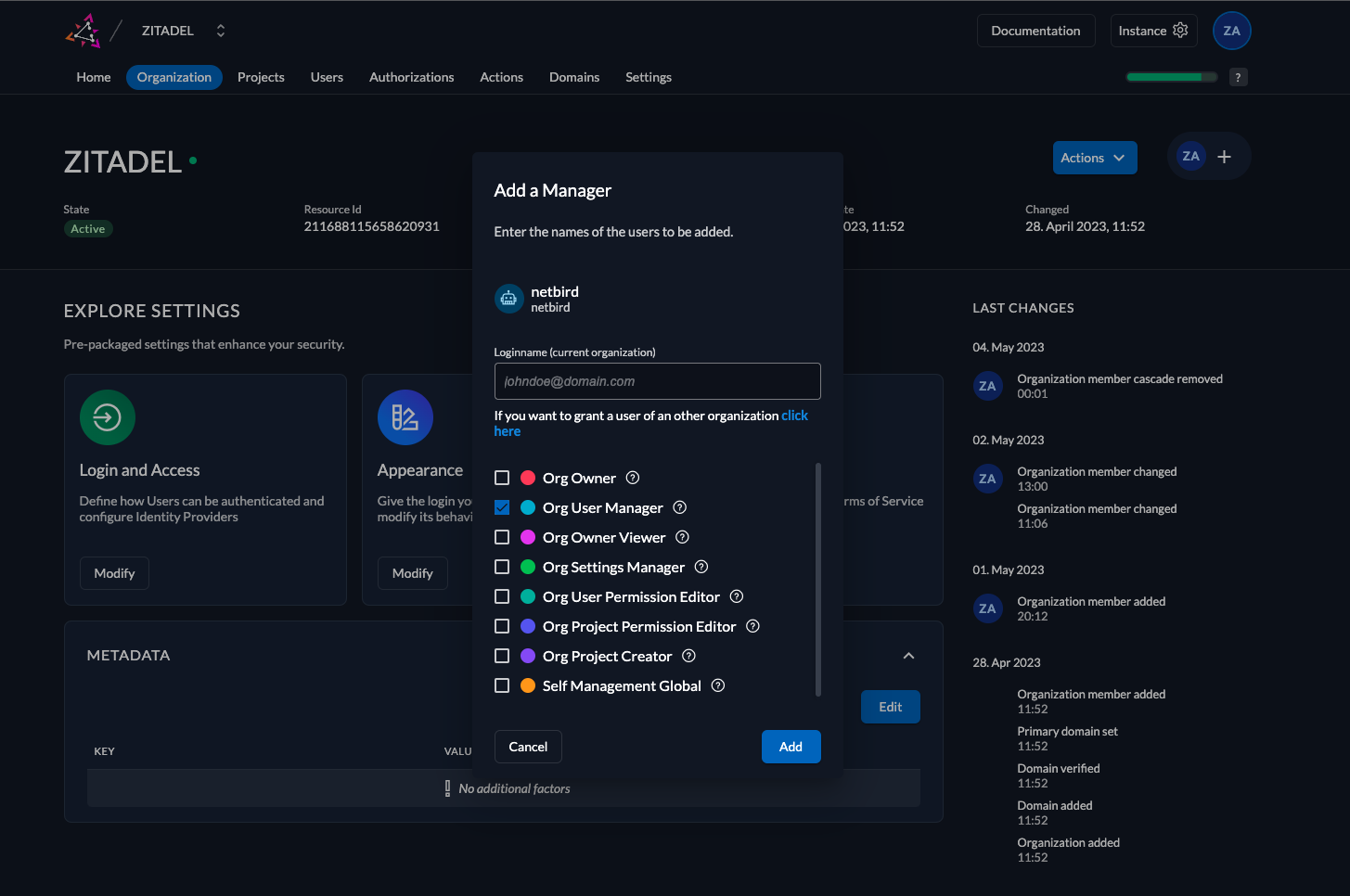
Step 5: Grant User Manager Role
- Click Organization in the top menu
- Click + in the top right corner
- Search for
qufabricservice user - Check Org User Manager checkbox
- Click Add
Step 6: Configure QuFabric
Your authority OIDC configuration will be available at:
https://<YOUR_ZITADEL_HOST_AND_PORT>/.well-known/openid-configuration
Double-check if the endpoint returns a JSON response by calling it from your browser.
Set properties in the setup.env file:
QUFABRIC_AUTH_OIDC_CONFIGURATION_ENDPOINT="https://<YOUR_ZITADEL_HOST_AND_PORT>/.well-known/openid-configuration"
QUFABRIC_USE_AUTH0=false
QUFABRIC_AUTH_CLIENT_ID="<CLIENT_ID>"
QUFABRIC_AUTH_SUPPORTED_SCOPES="openid profile email offline_access api"
QUFABRIC_AUTH_AUDIENCE="<CLIENT_ID>"
QUFABRIC_AUTH_REDIRECT_URI="/auth"
QUFABRIC_AUTH_SILENT_REDIRECT_URI="/silent-auth"
QUFABRIC_AUTH_DEVICE_AUTH_PROVIDER="hosted"
QUFABRIC_AUTH_DEVICE_AUTH_CLIENT_ID="<CLIENT_ID>"
QUFABRIC_AUTH_DEVICE_AUTH_AUDIENCE="<CLIENT_ID>"
QUFABRIC_MGMT_IDP="zitadel"
QUFABRIC_IDP_MGMT_CLIENT_ID="qufabric"
QUFABRIC_IDP_MGMT_CLIENT_SECRET="<CLIENT_SECRET>"
QUFABRIC_IDP_MGMT_EXTRA_MANAGEMENT_ENDPOINT="https://<YOUR_ZITADEL_HOST_AND_PORT>/management/v1"
QUFABRIC_MGMT_IDP_SIGNKEY_REFRESH=true
Step 7: Continue with QuFabric Setup
You've configured all required resources in Zitadel. Continue with the QuFabric Self-hosting Guide.
Migrating from Zitadel Quickstart
If you deployed QuFabric using the previous quickstart script with Zitadel:
Option A - Keep using Zitadel standalone: Continue with your existing setup. No changes needed.
Option B - Add Zitadel as external IdP directly in QuFabric Management Dashboard:
- Deploy new QuFabric version with embedded IdP
- Add your existing Zitadel as an external IdP directly in the QuFabric Management Dashboard (follow Management Setup above)
- Users can continue logging in with Zitadel
- Optionally create local user accounts as fallback
Option C - Migrate fully to embedded IdP:
- Export user list from Zitadel
- Deploy new QuFabric version with embedded IdP
- Recreate users in QuFabric Dashboard
- Decommission Zitadel when ready
Troubleshooting
"Token validation failed" error
- Verify the issuer URL is correct
- Ensure User Info inside ID Token is enabled
- Check that the audience matches your client ID
Service user authentication fails
- Verify the client secret was copied correctly
- Ensure the service user has Org User Manager role
Device auth not working
- Ensure Device Code grant type is enabled
- Verify PKCE is configured for the application

